EMAIL SUPPORT
dclessons@dclessons.comLOCATION
USConfigure Layer 2 Interfaces
From Cisco NX-OS 5.2 Releases onwards there are fooling types of Layer 2 ports configurable on Nexus Device
- An Access port
- A Trunk Port
- A Private VLAN ports
- A fabric Path Port
- A Shared Interface: But you cannot configure access port as shared interface.
Access Port:
An access port are those port where any host are connected and are part of only one VLAN. To optimize access port performance, you can also configure access port as host port. If any access port receives any packet tagged with 802.1Q value in header other than access VLAN value, port will not learn the MAC address of the packet and simply drops the packet.
N7K1# configure terminal
N7K1(config)# interface ethernet 1/1
N7K1(config-if)# switchport mode access
N7K1(config-if)# switchport access vlan 10
Configure HOST Port:
N7K1# configure terminal
N7K1(config)# interface ethernet 1/1
N7K1(config-if)# switchport host
Trunk Port:
A trunk port are those ports through which one or more than one VLAN traffic or VTP information, Broadcast packet can pass through. A trunk port can be part of multiple vlan. Cisco Nexus series switches support only 802.1Q encapsulation for tagging any vlan traffic which are going out of any trunk port.
By default all ports on Nexus 7K are layer 3 interface. You can convert all ports to layer 2 ports by following command: system default switchport
A trunk port can also be configured to specifically allow certain VLAN to flow over it by following command:
Switchport trunk allowed vlan add < VLAN IDs >
IEEE 802.1Q Encapsulation:
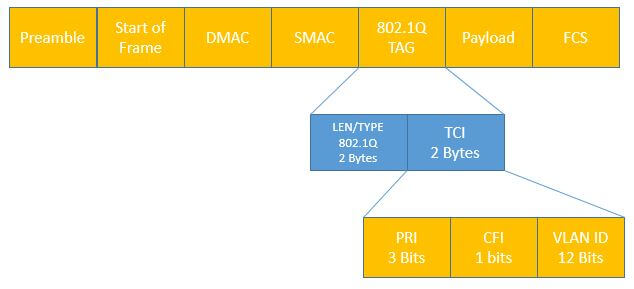
A trunk port is the port which carry traffic of multiple Vlans, in order to mark or identify which packet belong to which vlan tagging is done. This tagging is done by inserting the 4 byte tag in to frame header. This tag provide the information about specific VLAN of which this packet belong to.
Access VLAN:
Access VLAN are those VLAN which are used to configure any access port. Any Access port who are part of any access VLAN, will carry the traffic of that VLAN only. If any port not configured in any access VLAN are by default part of VLAN 1.





LEAVE A COMMENT
Please login here to comment.