EMAIL SUPPORT
dclessons@dclessons.comLOCATION
USAttaching Devices to VPC Domain
How to connect the device with vPC domain:
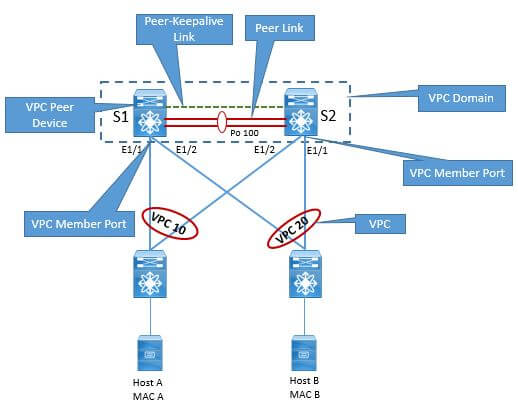
A device can be connected to vPC domain by creating the Layer2 port-channel from access device to VPC peer device. The below figure briefly explain the topology and its component involved.
Layer-3 Port channel is not supported with vPC topology.
Following are the requirement for access device to properly connect to vPC domain:
- Device should support 802.3ad LACP capability
- Device also support static port-channel (Channel-group mode on)
Cisco Nexus 7000 series switch does not support Port-aggregation protocols (PAgP). If the downstream access switch is a Cisco Nexus device, enable the LACP graceful-convergence option (this option is ON by default).
If the downstream access switch is a not a Cisco Nexus device, disable the LACP graceful-convergence option.
Use source-destination IP, L4 port and VLAN as fields for port-channel load-balancing hashing algorithm. This improves fair usage of all member ports forming the port-channel.
Access device dual attached to vPC domain:
In order to attach the access device to vPC domain, following topology can be used as a sample:
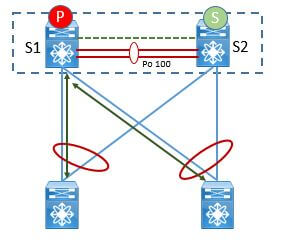
But there are two major topology to design vPC system. We have already discussed these topology:
- Singe sided vPC
- Double sided vPC
In single sided vPC a access device can be dual attached to vPC domain by 16 ports (8 ports to one vPC peer and another 8 ports to another vPC peer)





LEAVE A COMMENT
Please login here to comment.