EMAIL SUPPORT
dclessons@dclessons.comLOCATION
USLayer 3 Outside & External Routed Networks
Layer 3 connectivity to networks that reside outside ACI (are not directly connected to ACI fabric) requires configuration of a Layer 3 external outside network (l3extOut) interface. On the interface, peering protocol is configured along with route redistribution and inbound/outbound filtering and classification rules. All these parameters are associated with a special "external" EPG.
External subnets are classified as EPGs but are based on network address and subnet mask, not on parameters that are used for internal EPGs. When the traffic is assigned to EPG, it cannot pass without a proper contract between internal and external EPG.
Propagation of internal subnets to external network requires additional parameter to be defined, but not on outgoing interface but rather on BD where subnets are defined. There are some options to limit what will be propagated outside the ACI fabric, but are not so commonly used.
L3Out is used for routing configuration, which provide the Routing of Bridge domains subnets. L3Out Policy is used to configure interface, routing protocols and its parameters which is necessary to provide IP connectivity to external routing devices. L3Out connection is configured by External Routed network option for a tenant in APIC and is associated with VRF.
L3Out configuration includes defining of external networks specifically or external network can be defined as 0.0.0.0/0 to cover all possible destination
Once the External network is defined, contracts are configured between internal EPG and External EPG for proper traffic flow between them.
Below figure well explains the working object model for L3out and helps in understanding the main building blocks of L3out model.
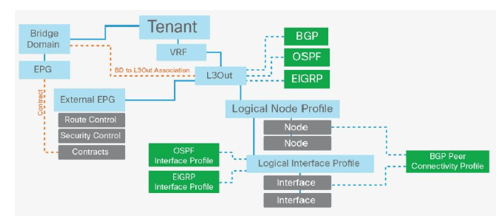
When L3out policy is associated with a VRF it consists the following:
- Logical Node Profile: This is Leaf wide VRF routing configuration (dynamic or static routing), if you have two border leafs then the logical node profile consists of two nodes.
- Logical Interface Profile: This includes L3 Interface or SVI configuration on leafs defined by logical node model. Interface selected by the logical interface profile must have been configured with a routed domain in the fabric access policy. This routed domain may also include VLANs if the logical interface profile defines SVIs.
- External network and EPG: This object classifies traffic from outside in to a security zones.
The L3Out connection must be associated with bridge domain whose subnets needs to be advertised to the outside ACI fabric.
Route Announcement Options for the Layer 3 Outside:
When configuring the subnets under bridge domain or an EPG for given tenant, following scopes can be selected based on requirement:
- Advertised Externally: This subnet is advertised to the external router by the border leaf.
- Private to VRF: This subnet is contained within the Cisco ACI fabric and is not advertised to external routers by the border leaf.
- Shared Between VRF Instances: This option is for shared services. It indicates that this subnet needs to be leaked to one or more private networks. The shared-subnet attribute applies to both public and private subnets.
Those subnets which are configured in bridge domain and are announced to outside router only when following conditions are met:
- The subnets must be defined as advertised externally.
- The bridge domain must have a relationship with the L3Out connection and is associated with the VRF instance.
- A contract must exist between the Layer 3 external EPG (external subnets for the external EPG) and the EPG associated with the bridge domain. If this contract is not in place, the announcement of the subnets cannot occur.
- When defining a L3Out configuration, the route control export option is automatically selected. You define which subnets are announced from the L3Out to the outside by configuring the default-export route map.
Although we can control which of the outside networks learned through the L3out are imported in to ACI fabric and it can be done by using the default-import route-map configuration under the L3Out.
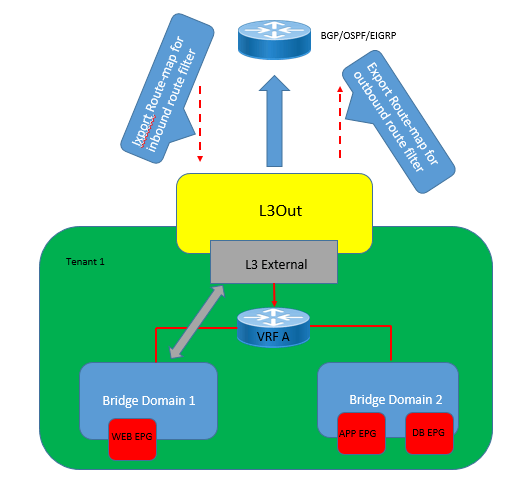
These Route map are applied to all routes:
- Directly connected subnets
- Static routes
- Transit routes
External Network (External EPG) Configuration Options:
External EPG contains external endpoints or external routes based on IP Prefixes or Host address. One or multiple external EPGs can be associated with one L3out connection based on whether different policy treatments are needed for different groups of external endpoints.
Following are the summery of the options available for external network configuration and function they perform.
- Subnet: This defines the subnet used to define the external EPG classification.
- Export Route Control Subnet: This configuration controls which of the transit routes (routes learned from another L3Out) should be advertised. This is an exact prefix and length match. ( Learn More in L3-Out Subnet Flag Section)
- Import Route Control Subnet: This configuration controls which of the outside routes learned through BGP should be imported into the fabric. This is an exact prefix and length match. ( Learn More in L3-Out-Subnet Flag Section)
- External Subnets for the External EPG: This defines which subnets belong to this external EPG for the purpose of defining a contract between EPGs. ( Learn More in L3-Out-Subnet-Flag Section)
- Shared Route Control Subnet: if network is learned from the outside through this VRF, it can be leaked to the other VRFs if they have a contract with this external EPG.
- Shared Security Import Subnets: This defines which subnets learned from a shared VRF belong to this external EPG for the purpose of contract filtering when establishing a cross-VRF contract. This configuration matches the external subnet and masks out the VRF to which this external EPG and L3Out belong.
- Aggregate Export: This option is used in conjunction with Export Route Control Subnet and allows the user to export all routes from one L3Out to another without having to list each individual prefix and length.
- Aggregate Import: This allows the user to import all the BGP routes without having to list each individual prefix and length. With Aggregate Import, you can simply allow all BGP routes.
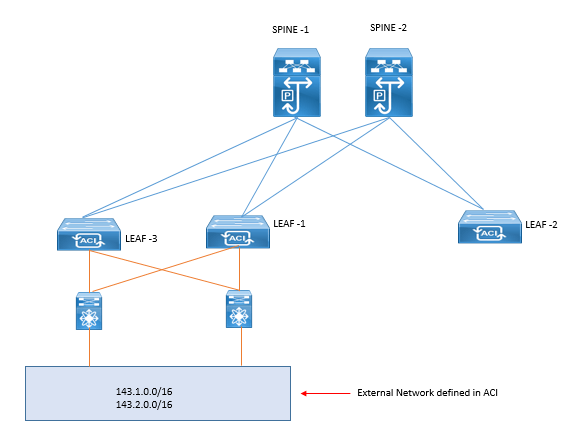
Border Leaf Switch Designs
Border leafs are used to provide the layer 3 connection to outside networks, It provide or supports three types if interfaces to connect to external router.
- Layer 3 (routed) interface
- Sub interface with IEEE 802.1Q tagging: With this option, multiple sub interfaces can be configured on the main physical interface, each with its own VLAN identifier.
- Switched virtual interface: With an SVI, the same physical interface that supports Layer 2 and Layer 3 can be used for Layer 2 connections as well as an L3Out connection.
Following are the routing protocols that border leafs or ACI supports:
- Static routing (supported for IPv4 and IPv6)
- OSPFv2 for regular, stub, and not-so-stubby-area (NSSA) areas (IPv4)
- OSPFv3 for regular, stub, and NSSA areas (IPv6)
- EIGRP (IPv4 only)
- iBGP (IPv4 and IPv6)
- eBGP (IPv4 and IPv6)
L3Out with VPC:





LEAVE A COMMENT
Please login here to comment.