ISE Introduction
Architecture approach to Network Security Policy Enforcement:
In relation to Centralized and dynamic Network Security Policy Enforcement prior to 2004 Cisco has product named NAC and we say as Cisco NAC Solution and it was based on 802.1X and integration with network services , but it was not widely deployed.
In 2011 Cisco developed and released Cisco ISE to provide 802.1X based NAC solution to its customer and since 2011 ISE has been aggressively evolved with more and more and rich feature set.
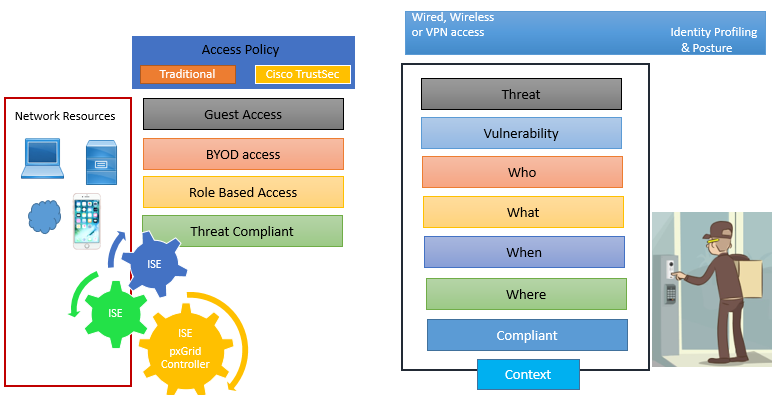
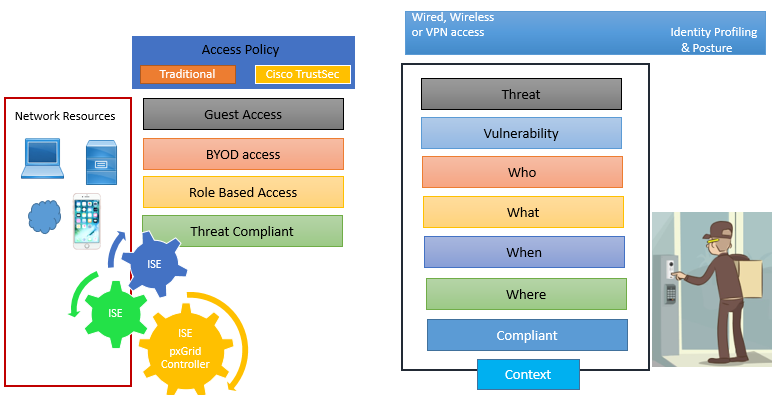
Below figure describe how ISE works in nutshell.
ISE feature & Benefits:
Below is the composite feature and benefits of Cisco ISE.
Centralized Management: We can centrally configure, manage profile, posture, guest, authentication & authorization, via single web based GUI console.
Business Policy Enforcement: For business-relevant access control policy it provides rule based and attribute driven policy. Various attributes includes user, end point identity, posture validation, authentication protocols, profiling identity, etc. These attributes can be created dynamically and saved to use later.
It integrates with various third party external identity repository like LDAP, AD, RADIUS, certificate authority.
Access Control: It provides various access control options like dACL, VLAN assignment, URL redirection, named ACLs, SGTs.
Secure Supplicant-less network access with Easy Connect: It derives authentication & authorization from login information across application layers.
Guest Lifecycle Management: Its helps in achieving Guest Lifecycle management from guest authentication to guest onboarding and guest security policy compliance. Time limits, account expiration, SMS verification are some services provided by ISE.
Streamline Device Onboarding: It enables user to add and manage their devices with self-service portal and supports SAML 2.0 language for web portal.
It also integrates with MDM/EMM vendors to enroll mobile device and ensure that those device are compliant with security policy.
AAA Services: It uses RADIUS protocols for authentication, authorization and accounting. It also supports wide range of authentication protocols like PAP, CHAP, EAP-MD5, EAP (PEAP), EAP-FAST, EAP-TLS, and EAP-TTLS.
Device administration access control and auditing: Uses TACACS+ protocols for authentication, authorization and accounting users when they access device that supports TACACS+ protocols.

GENERAL FAQ
Cisco Identity Services Engine (ISE) is a centralized security policy management platform that enables enterprises to enforce compliance for wired and wireless devices. In brief, it keeps your enterprise locked down by authenticating users, authorizing access, and maintaining compliance.
The Cisco Identity Services Engine (ISE) is a centralized network access control and policy enforcement platform. With Cisco ISE, centralized policy management to control network access and usage policies can be performed from a single management interface.
Cisco ISE gathers key information about user and device access and uses this information to control end-user network access and administrative network device access, regardless of connection type. Wired, wireless, and remote users can connect directly to the physical or wireless network, or they can connect through virtual private networks (VPNs). Whether connected remotely or directly to corporate resources, users can receive the same unified access and control.
Cisco ISE also delivers guest and enterprise mobility management capabilities that regulate access to the Internet as well as the internal network and company files. You can set up automatic rules to offer employee sponsorships. This automation helps you maintain overall corporate security and ensure that guests and contractors get timely access.
Cisco ISE can also use gathered information to ensure regulatory compliance with various government and industry standards. This information can be shared among Cisco Ecosystem partner devices using Platform Exchange Grid (pxGrid) or application programming interfaces (APIs). The sharing of this data is used to enhance the capabilities for services, including security information and event management (SIEM), mobile device management (MDM), network behavior analysis (NBA), intrusion prevention systems (IPS), and much more.
Cisco ISE (Identity Services Engine) is a more advanced and comprehensive successor to Cisco NAC (Network Admission Control), offering broader capabilities, better scalability, and deeper integration for modern network environments.
Before the ISE, the Cisco access solution was NAC (Network Admission Control). Use of NAC was restricted and not so common. From 2011, this has been replaced by Cisco ISE - a more flexible, scalable, and feature-rich system that can do 802.1X as well as authenticate against identity services such as LDAP or Active Directory.
The ISE master class is about major capabilities of the ISE: centralized management, guest access, posture validation, profiling and device onboarding, policy enforcement, and more. You will also get introduced to AAA, TACACS+, and RADIUS while being shown how Cisco ISE works with MDM systems to keep your mobile devices meeting compliance.
This course is intended for network and security engineers who wish to understand the access controls in place in modern enterprise networks and the policies used to govern those controls. Aids professionals training for Cisco certification or who manage secure user access daily.
The course focuses on both. You will get a clear concept about how ISE works and what its features look like as guest management, device onboarding & dynamic access control implemented under enterprise networks.
You will examine various ISE-supported authentication protocols such as PAP, CHAP, EAP-MD5, PEAP, EAP-FAST, EAP-TLS, and EAP-TTLS. You’ll also learn how ISE can leverage RADIUS and TACACS+ for Authentication, Authorization, and Accounting in network deployments.





LEAVE A COMMENT
Please login here to comment.