EMAIL SUPPORT
dclessons@dclessons.comLOCATION
USISE Device Profiling
Device Profiling is built in function of ISE. It collect active and passive data of device including device behavior, Device activity etc. With the help of device profiling, we are able to see what are all devices connected to network, Device Type, their behavior & Activity and the logged in user.
Profiling includes large number of built-in profiling rules, and its profiler condition. These rules are updated dynamically by using profiler Feed Service.
Now whatever information is collected of any device are matched with these conditions until best condition are matched. Once the condition is best matched, then that condition is matched to profiler policy rule, and once the policy profiler rule is matched, the result is used as an ISE authorization rule condition.
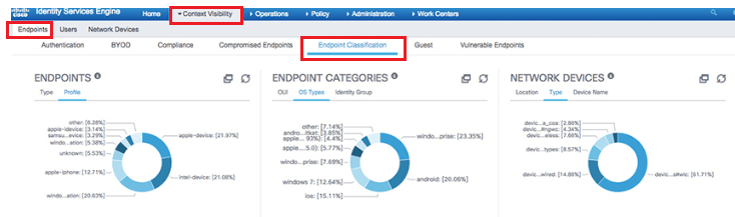
Below figure describes ISE profiler Endpoint Context Visibility.
Below figure describes ISE profiler condition that are pre-installed in ISE. ISE also receives and updates the new profile via ISE profiler Feed Service. This Feed Service connect to Cisco.com for new updates.
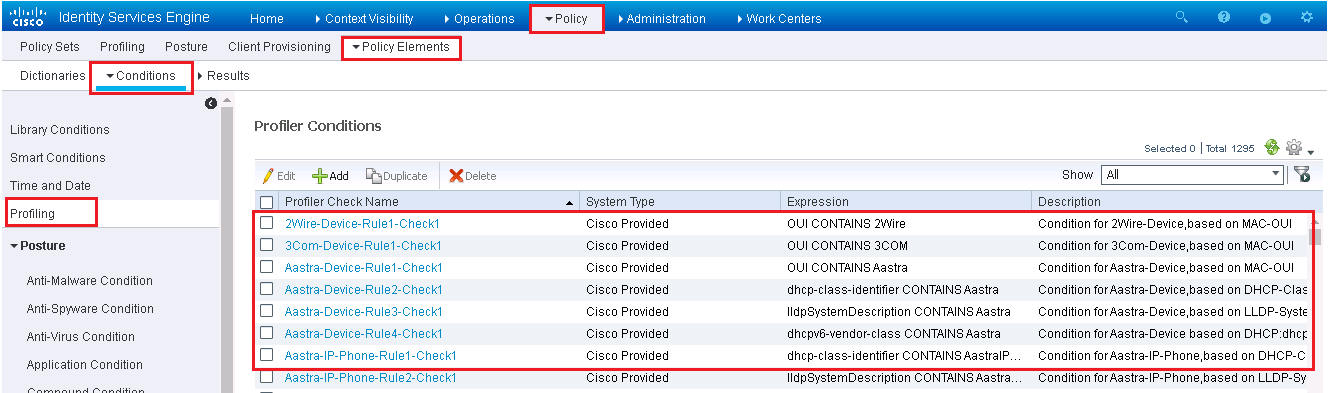
Each condition has a logic, which is used to match with device attributes. Many condition have multiple rules of checks for same device type. Below figure is used for Apple iPad profiler condition which has four checks in order to verify weather device is iPad or not.
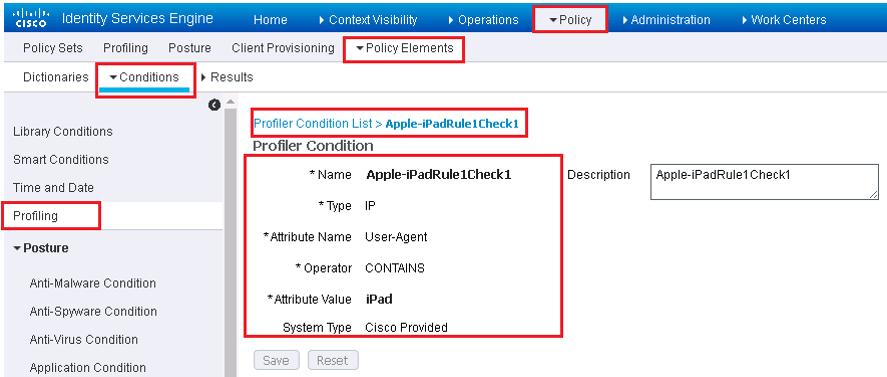
The above figure, condition shown matches the user-agent string from web browser.
ISE Profiling Policies
Using same example of Apple iPad profile, below figure shows profiler policy that uses the iPad condition
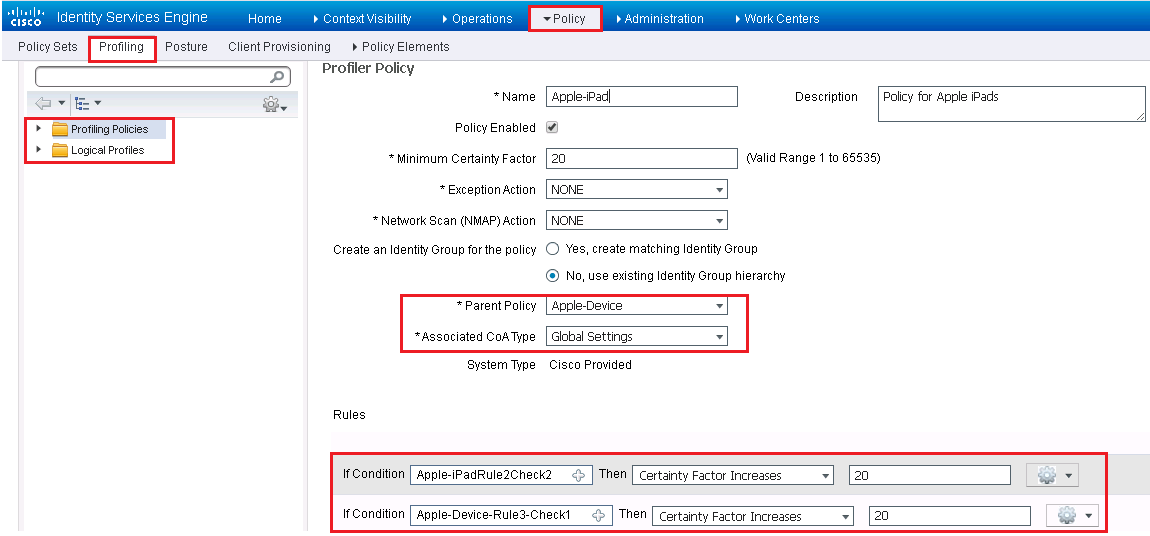
In the above figure, policy uses two rule. If both rule are matched, it will raise the certainty factor value by 20. This profiler policy defines that minimum Certainty factor to be matched is 20.
For any custom related profile, the policy should include following parameters:
Device Profile Conditions Definition: includes values like User-agent string, MAC, OUI, DHCP, Hostname for match criteria.





LEAVE A COMMENT
Please login here to comment.