EMAIL SUPPORT
dclessons@dclessons.comLOCATION
USClient Posture Assessment
With the help of ISE posture assessment method, we can check and know whether our clients are in compliance with organization Host security policy. It check the security health of PC, and Mac Clients
Below are some example that ISE posturing feature check for clients.
- OS Installation Status
- Machine running state
- Security Software last update
- Anti-Virus Status
- Anti-Malware Status
- Personal FW state
- Host OS patch status
- Checks for custom attributes like Files , Processes , Registry , Setting & Applications
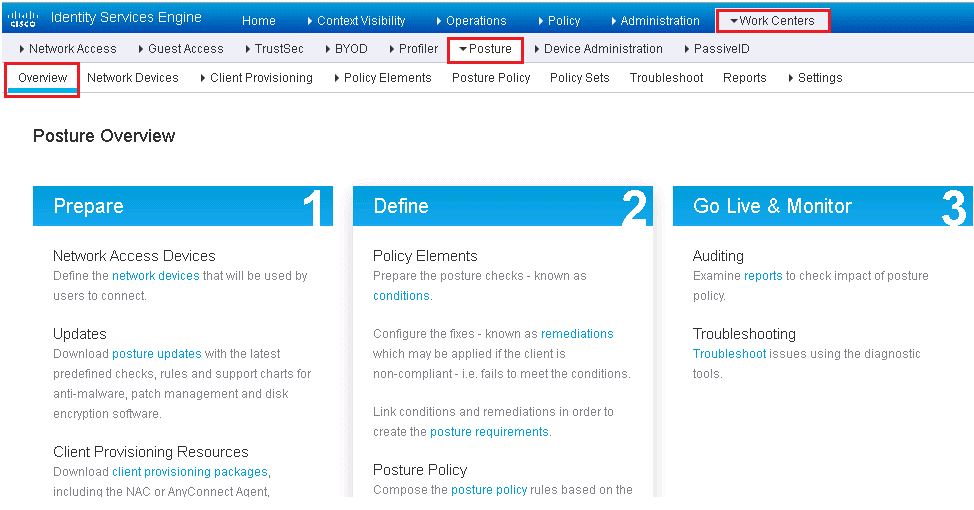
ISE has design specific Work center for configuring various components of Posturing Solutions in its WorkCentre.
Below are following three steps which are required to configure Posturing in ISE.
- Prepare
- Define
- Go-Live & Monitor
Below are some high-Level steps required to setup ISE posturing assessment feature
- Configure global posture and client provisioning settings:
- Download to ISE the latest posture updates and the client provisioning packages.
- Verify the default global posture settings meet your needs.
- Configure the posture client provisioning policy.
- Configure the Client Provisioning Portal.
- Configure posture elements:
- Configure posture conditions.
- Configure posture remediation.
- Configure posture requirements.
- Configure posture policy.
- Optionally, configure host application visibility and context collection.
- Enable posture client provisioning and assessment in your ISE authorization policies.
- Enable posture assessment on the network devices.
ISE Posture Assessment Flow
In order to understand the IE posturing, we need to understand the ISE flow that ISE undergoes when Posturing Assessment is enabled.
Below figure describes the ISE Flow when Posturing is enabled.
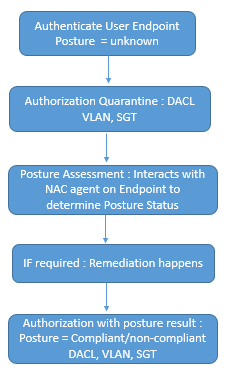
Below are steps description
AT first 802.1X Suppliant Client talks to access layer switch to start 802.1X. EAP transaction starts between Clint and ISE and switch is acting as Proxy here. If Authentication is successful posture status is set to unknown.
ISE instruct Switch to redirect client to ISE URL. Which will help client to download the Posture NAC agent or dissolvable NAC agent software on client based on policy.
Once NAC agent is downloaded to Client, It will use SWISS protocol to communicate with ISE and at end, Posture result is created.
ISE will send the CoA request to switch, which will starts the 802.1X re-authentication , and a New authorization rule is matched to provide new result about client , which says that cline is compliant or non-Compliant. Now here new access rights of match authorization rule are downloaded to switch.
If Periodic re-assessment is enabled, Client will be checked for regular posture assessment in any changes is done. If any status changes then CoA is issued again same steps will be followed.
Configuring Global Posturing & Client Provisioning Setting
Here global setting is to be enabled in order to turn on Posture assessment. It is done by two parts.
- Client Provisioning Setup: which deals with NAC agent software, its delivery and other setting.
- Posture setup: It helps in downloading posture condition DB and Clients, Keeping it Up to date, Posture reassessment, and general setting.
Client posturing global Setup
To configure and setup Client posturing global Setup, you should download and enable your posture resources. Below are three type of agents required for posture assessment, and each of which supports windows, Mac OS systems.
- Cisco AnyConnect with the compliance module
- Cisco NAC Agent
- NAC Web Agent
Below are the list of all client provisioning resource type
- Persistent and temporal posture agents:
- Windows and Mac OS X Cisco AnyConnect Agents with the ISE compliance module installed
- Windows and Mac OS X Cisco NAC Agents
- Cisco NAC Web Agent
- Agent compliance modules
- Agent customization packages
To enable and download the posture resources: Administration | System | Settings | Client Provisioning, Make sure that ISE proxy setting are enabled before doing any configuration.
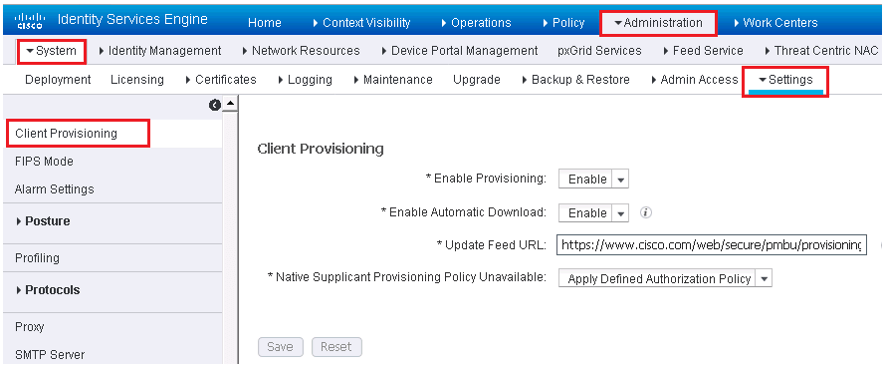
In the above figure, follow below steps:
- Enable Client Provisioning
- Enable automatic downloads which is optional. Enabling it will enable any or all client files from Cisco.com. You can select the exact files which is required. In this use the default feed URL or set up your own client repository site.
- Keep the default setting of Allow Network Access for native suppliant provisioning field.
- Click Save.
In order to select the Client files, go to Policy | Policy Elements | Results | Client Provisioning | Resources.
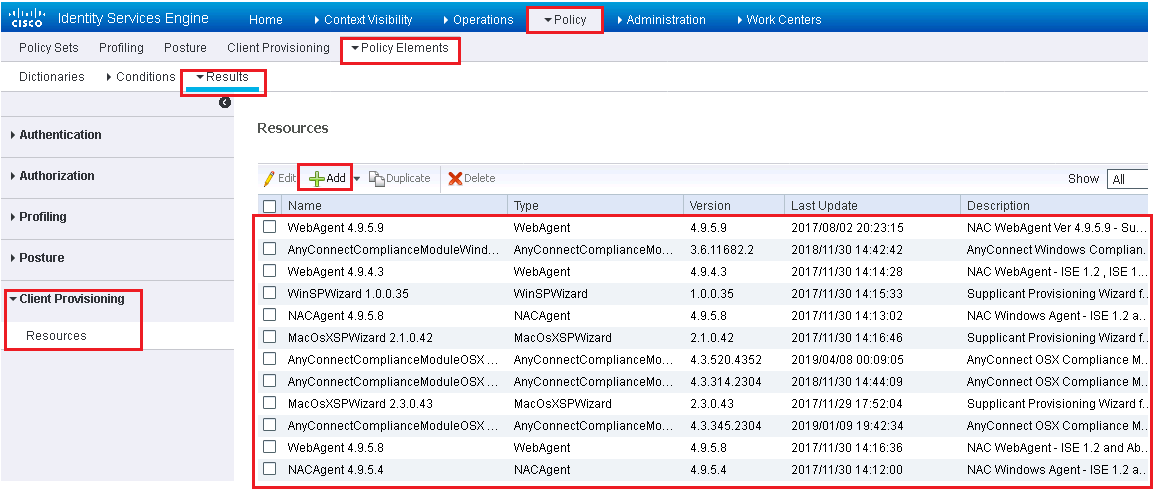
Above figure show you all the agents and other ISE resources that has been downloaded already. If you need to add more, Click on ADD and choose to add them from Cisco.com. or from local PC and then click Save.
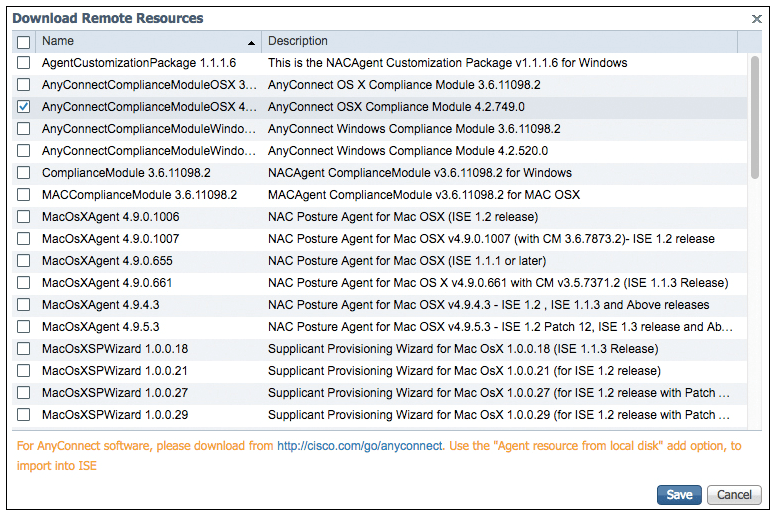
Now see the below figure , it will tell you that you can only download the Any connect compliance Module that fits inside the full Any Connect Client and you cannot download the full AnyConenct Agent from ISE ( On ISE Version 2.2). If you still want to download the full version, go to Cisco.com/go/AnyConnect. Below fig correctly describes what to download. (AnyConnect Headend Deployment Package (.pkg) files.





LEAVE A COMMENT
Please login here to comment.