EMAIL SUPPORT
dclessons@dclessons.comLOCATION
USISE Building blocks & Design
ISE Solution Components:
There are three ISE solution components to complete Cisco ISE Design Architecture.
- Infrastructure Components
- Policy Components
- Endpoint Components
Infrastructure Components:
Devices such as Wireless, WLC, Switches, Routers, Firewall, VPN, AD, LDAP etc which uses ISE to create secure access infrastructure. Full ISE functionality on both Cisco and Non-Cisco devices are supported in ISE2.0 version.
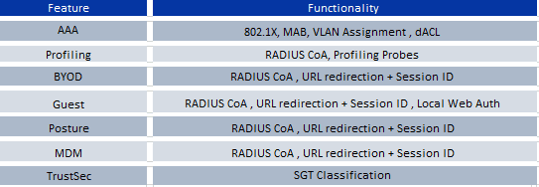
Below is feature to functionality mapping that ISE uses.
Below table shows partial mapping of ISE supported devices to ISE features and it also states the minimum OS levels for each devices that to be used with ISE.
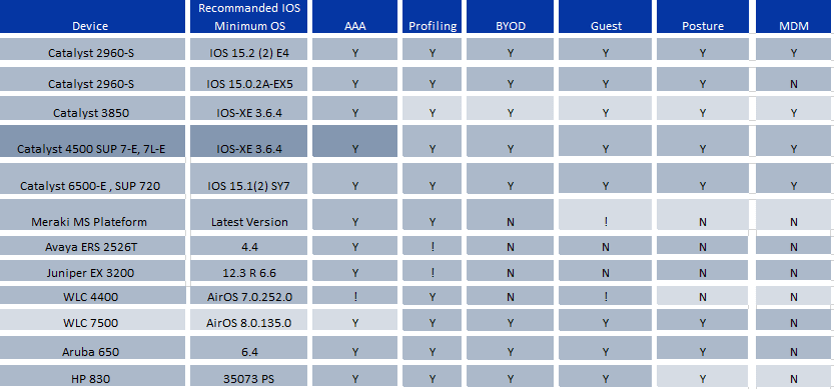
In the above table! Stands for Limited support.
Policy Components:
Cisco ISE provides access control management on Wire, Wireless and Context based environment. Policy components can be spanned in following areas.
- ISE checks and determines that user accessing network are authorized and have policy compliant device.
- ISE establish user identity, location, access-history, for compliance and reporting
- ISE assigns policy and service based on user host and user context example assigns user to role, AD group, location, device type.
- ISE allows authenticated users to access specific segments of network or specific applications, services or both.
Endpoint Components:
Endpoint are those identity that access the network , access the application and services and for this they authenticates to ISE using 802.1X, MAB , Easy Connect or web authentication.
Following are recommended Endpoint components:
802.1X supplicant/agents: A suppliant is built on Windows or Mac OS X and is just software that understand how to communicate via EAPoL (Extensible Authentication protocol over LAN). Supplicant is also available via Cisco AnyConnect or via any other third party suppliant software agents. Some suppliant is in build with certain hardware like IP phone, Video equipment, printers.
Cisco AnyConnect Compliance Module: With the help of this module all windows , Mac OS X , Linus systems provides host posture information to ISE like antivirus installed status, OS patching , presence of registry keys.
ISE Personas:
ISE can be deployed in two mode:
- Standalone deployment mode : In this all Personas are on a single ISE appliance or a pair of ISE appliance
- Distributed deployment mode: Personas are spread out and dedicated to just particular ISE appliances.
ISE has three personas and each personas type ISE node determines that service it provides.
Administration:
- It allow to perform all administrative operation in standalone or distributed ISE deployment
- It provides a single pane of glass for management and all system related and policy-based configuration can be done from this Personas
- In distributed deployment model, it can be single ISE or can be in HA pair of nodes running administration Persona.
- The ISE node working as administration Personas is called as Policy Administration Node(PAN)
Policy Service:
This Personas type has following features:
- It provides network access, posture, guest access and client provisioning, web portals and profiling services Policy service Personas can be deployed in more than one node and when it has dedicated ISE node then it is referred as Policy Service Node (PSN)
- In Distributed environment, PSN can be more than one node and can be geographically separated to each other.
Monitoring:
Monitoring Personas helps in log collector, and store logs from PAN and PSN.
- This Personas provides advances monitoring and troubleshooting tools and is referred as Monitoring & Troubleshooting node (MnT)
- ISE allow only to have maximum of two nodes with this personas and both can take primary or secondary role for HA.
- Both node captures logs and if primary fails secondary automatically becomes primary monitoring node.
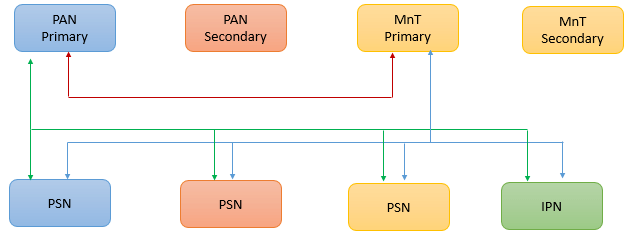
Below is the architecture which shows how these personas and node type look logically and here only primary connection are shown.





LEAVE A COMMENT
Please login here to comment.