EMAIL SUPPORT
dclessons@dclessons.comLOCATION
USAuthentication & Authorization Policies
Policy Set Enablement
AN Authorization policy can only be created once Authentication policy are in place. A policy set consist of separate pair of Authentication and Authorization rule for each use cases.
To see Policy Set, Refer below path on ISE.
Policy| Policy Set
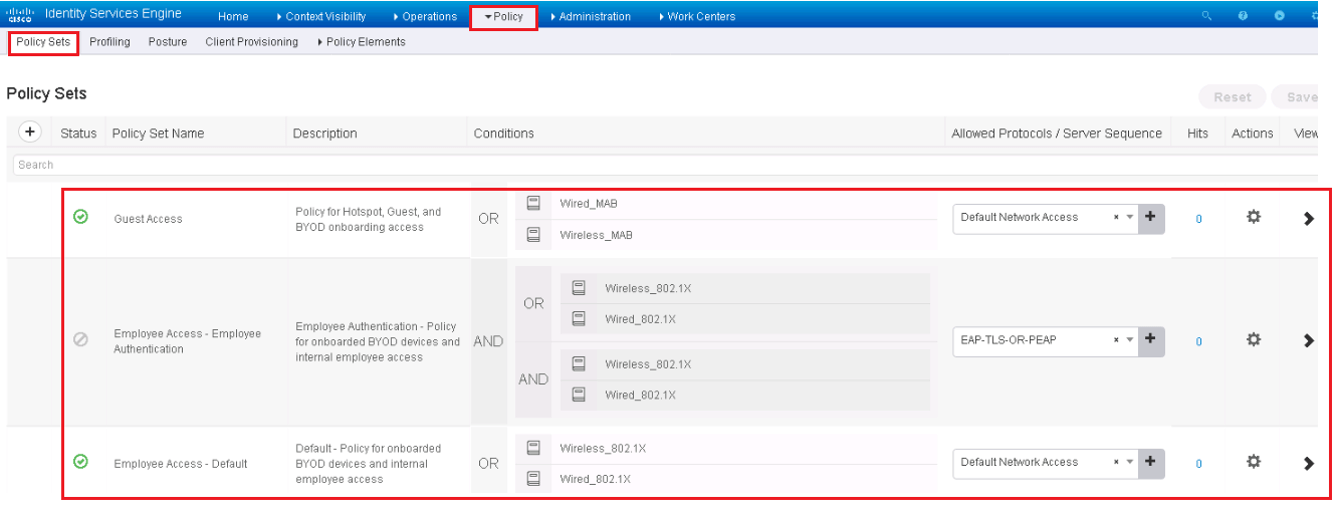
On the last, there is default policy, Click in default policy set, to see and verify the authentication and authorization policies.


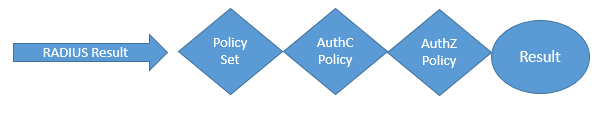
Below is the process , how policies are evaluated , as in figure Once RADIUS request are being made, and particular Policy Set is invoked , first authentication policy then authorization policy are processed to provide Result.
Authentication Policy Goals
Below are some goals that can be achieved by authentication Policy.
- To identify if the identity credential is valid or not.
- It drops incoming request who are not allowed
- It routes authentication request to correct identity store.
- Validate the identity
- Passes successful authentication request to the authorization Policy.
Authentication Policies Overview
Here we will see deep dive concepts about authentication policies. To go to authentication policy use following path:
- From the ISE GUI, navigate to Work Centers | Network Access | Policy Sets or Policy | Policy Sets
- A Basic Authentication policy rules are logically organize in following manner.
- IF conditions THEN ALLOW PROTOCOLS IN AllowedProtocolList
- AND CHECK THE IDENTITY STORE IN LIST IdentityStore
- In Authentication Policy, Rules are evaluated from top to bottom, the moment Match is found the evaluation is stopped else it will move to next rule.
Conditions: To understand this lets take an example, picturized below.
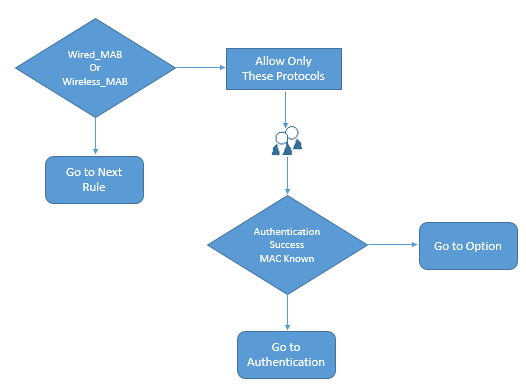
Condition checks if the user is Wired MAB or Wireless MAB, if yes then it will allow certain protocols defined. If Authentication success it will send to authorization policy else it will go to explore further options.
Navigate to Work Centers | Network Access | Policy Elements | Conditions | Smart Conditions
Select the Wired_MAB
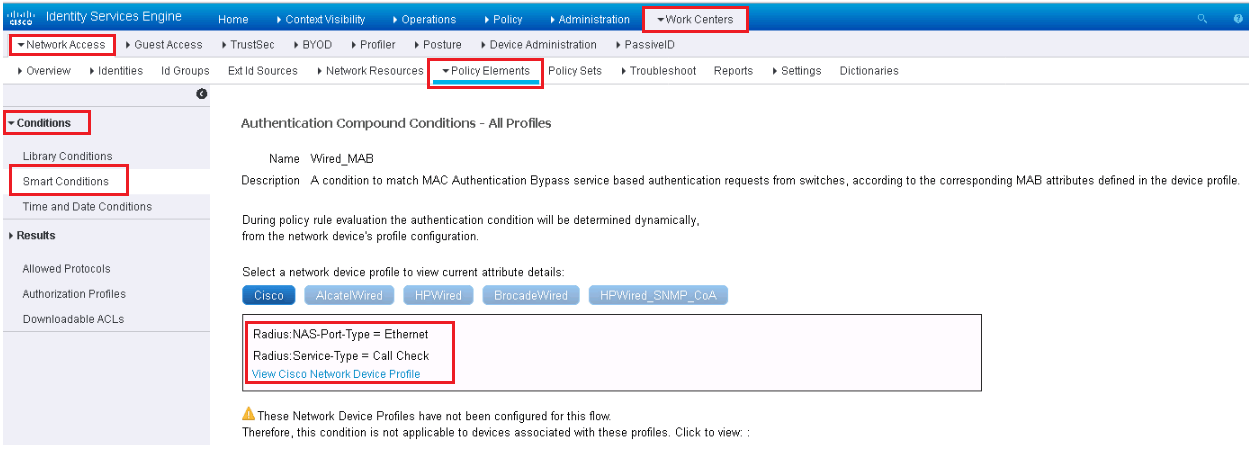
Here you can see, Condition Wired_MAB is mapped to different dictionary attributes per network device vendor.
For Cisco, the condition is looking for the RADIUS NAS-Port-Type to be Ethernet and Service-Type to be Call Check. These attributes are notified by RADIUS authentication packet to ISE, which indicates that this is MAB request from Switch.
Each different vendor has different attributes, and in order to see different vendor mapping, click on network device vendor name.
Now to see about Wireless MAB conditions,





LEAVE A COMMENT
Please login here to comment.