EMAIL SUPPORT
dclessons@dclessons.comLOCATION
USConfiguring Security Parameters
Configure Control Plane Security Parameters
Cisco Viptela device uses DTLS connection for control plane operation by default. DTLS uses UDP protocols. However it is possible to switch from DTLS to TLS connection after changing some configuration as TLS runs on TCP. The main reason to use TLS is that if you are using vSmart to be server, firewall protects TCP servers better than UDP servers.
To configure control plane tunnel protocol on a vSmart controller:
vSmart (config) # security control protocol tls
Once this configuration is done, all tunnel between vSmart and vEdge router and between vSmart to vManage will use TLS whereas connection to vBond will always be on DTLS.TLS will always take precedence over DTLS over scenario where large number of vSmart controller are there in domain and one vSmart controller TLS is configured. In this that vSmart will make TLS connection to all other vSmart controller and all other vSmart controller will make DTLS connection to all other vSmart controller except TLS vSmart controller.By default vSmart controller listen on 23456 for TLS, if required to be changed use:
vSmart (config)# security control tls-port number
Range: 1025 to 65535
To see the control plane security information, use following commands:
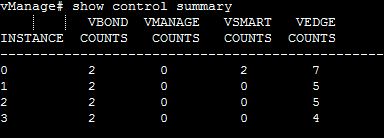
vSmart-# show control connections
if any plan is to configure TLS on vManage , as control plane protocols than enable port forwarding on NAT device and if you are using DTS than nothing is required.On vManage a process called vdaemon who is responsible for port forwarding and to see information about these process and about number of port being forwarded use following command:
To see the listening ports, use the show control local-properties command:
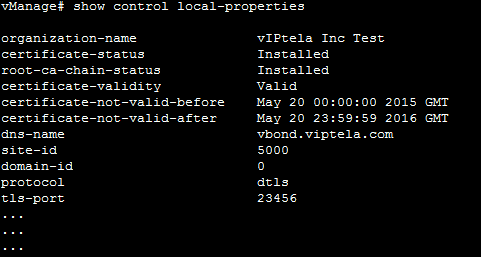
The above example shows it is using TLS port 23456 and if you are using vManage behind NAT, following ports needs to be opened on NAT device:
- 23456 (base - instance 0 port)
- 23456 + 100 (base + 100)
- 23456 + 200 (base + 200)
- 23456 + 300 (base + 300)
Configure Data Plane Security Parameters
For authentication, in data plane , IPSEC by default uses AH-SHA1 HMAC and ESP HMAC-SHA1.
Use following information to change parameters:
vEdge (config)# security ipsec authentication-type (ah-no-id | ah-sha1-hmac | none | sha1-hmac)
Details of these parameters are given below:
- ah-sha1-hmac enables following parameters such as AH-SHA1 HMAC and ESP HMAC-SHA1
ah-no-id enables a modified version of following parameters such as AH-SHA1 HMAC and ESP HMAC-SHA1. This option accommodates some non-Viptela devices such as Apple AirPort Express NAT. - sha1-hmac enables ESP HMAC-SHA1.
- None Provides no authentication
All vEdge router advertise their authentication type in TLOC properties and each negotiate and use strongest authentication type that is configured on both routers. if one vEdge router advertises AH-HMAC-SHA1, ESP HMAC-SHA1, and none, and a second vEdge router advertises ESP HMAC-SHA1 and none, the two routers negotiate to use ESP HMAC-SHA1 on the IPsec tunnel connection between them and if no authentication parameters are configured , no Ipsec tunnel is established.
There are two types of Encryption used in IPSec tunnel AES-256-GCM or AES-256-CBC. For unicast traffic if remote site support AES-256-GCM, that encryption algorithm is used. Otherwise, AES-256-CBC is used. For multicast traffic, the encryption algorithm is AES-256-CBC.
Change the Rekeying Timer





LEAVE A COMMENT
Please login here to comment.