EMAIL SUPPORT
dclessons@dclessons.comLOCATION
USDeploying Cisco SD-Access—Policy Workflow
Cisco DNA Center allows you to define policies that capture the business intent of your organization for specific aspects of the network, such as access control. These policies are automatically translated into device-specific configurations, tailored to the diverse types, models, operating systems, roles, and resource constraints of your network infrastructure.
Policy Application Workflows
The Policy application provides configuration workflows for:
- Group-based access control
- IP-based access control
- Application policies
- Traffic copy policies
- Virtual networks
Group-Based Access Control
Group-based access control policies are implemented as Security Group Access Control Lists (SGACLs). Cisco DNA Center integrates with Cisco Identity Services Engine (ISE) to streamline the creation and management of SGACLs.
- During initial integration, scalable groups and policies defined in Cisco ISE are automatically propagated to Cisco DNA Center and placed in the default virtual network.
- Cisco DNA Center does not support access control policies with logging actions. As a result, Cisco ISE does not propagate such policies to DNA Center.
- Depending on organizational requirements, scalable groups can be segregated into different virtual networks to achieve additional segmentation and policy granularity.
A group-based access control policy has two main components:
- Scalable groups: Scalable groups comprise a grouping of users, endpoint devices, or resources that share the same access control requirements. These groups (known in Cisco ISE as security groups) are defined in Cisco ISE. A scalable group may have as few as one item (one user, one endpoint device, or one resource) in it.
- Access contract: An access contract is a common building block that is used in both group-based and IP-based access control policies. Access contracts define the rules that make up the access control policies. These rules specify the actions (permit or deny) that need to be performed when traffic matches a specific port or protocol, as well as the implicit actions (permit or deny) to be performed when no other rules match.
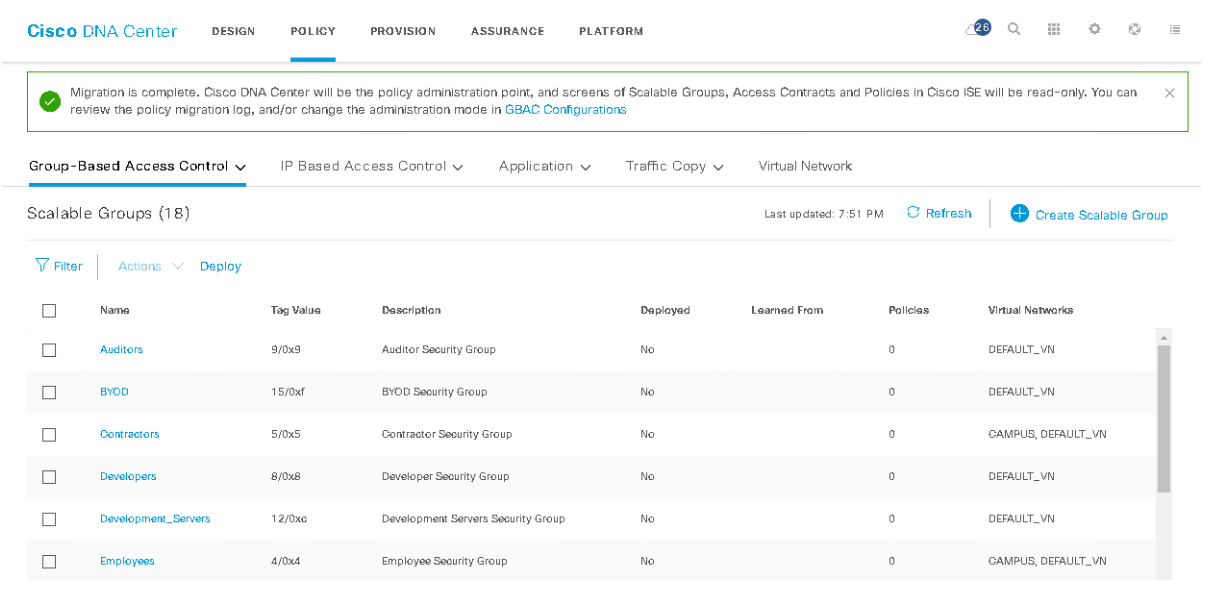
Before you can create group-based access control policies, make sure that Cisco ISE is integrated with Cisco DNA Center. Verify that the scalable groups have been propagated to Cisco DNA Center from Cisco ISE. To do this from the Cisco DNA Center home page, choose Policy > Group-Based Access Control > Scalable Groups. You should see scalable groups populated under the Scalable Groups tab. If you do not see any scalable groups, verify that Cisco ISE is integrated correctly. After you create a group-based access control policy, Cisco DNA Center translates the policy into an SGACL, which is ultimately deployed on a device.
The following sample procedure describes the process of authentication and access control that a user experiences after logging in to the network:
- A user connects to a port on a switch and provides credentials.
- The switch contacts Cisco ISE.
- Cisco ISE authenticates the user and downloads the SGACLs to the port to which the user is connected.
- The user is granted or denied access to specific users or devices (servers) based on the access granted in the SGACLs.
Group-based access control is based on Cisco TrustSec software. It relies on authentication, authorization, and accounting (AAA) services provided by Cisco ISE or third-party AAA or Network Admission Control (NAC) servers.
Cisco ISE is required to deploy group-based access control.
The following are the main building blocks of group-based access control:
- SGTs
- SGACL
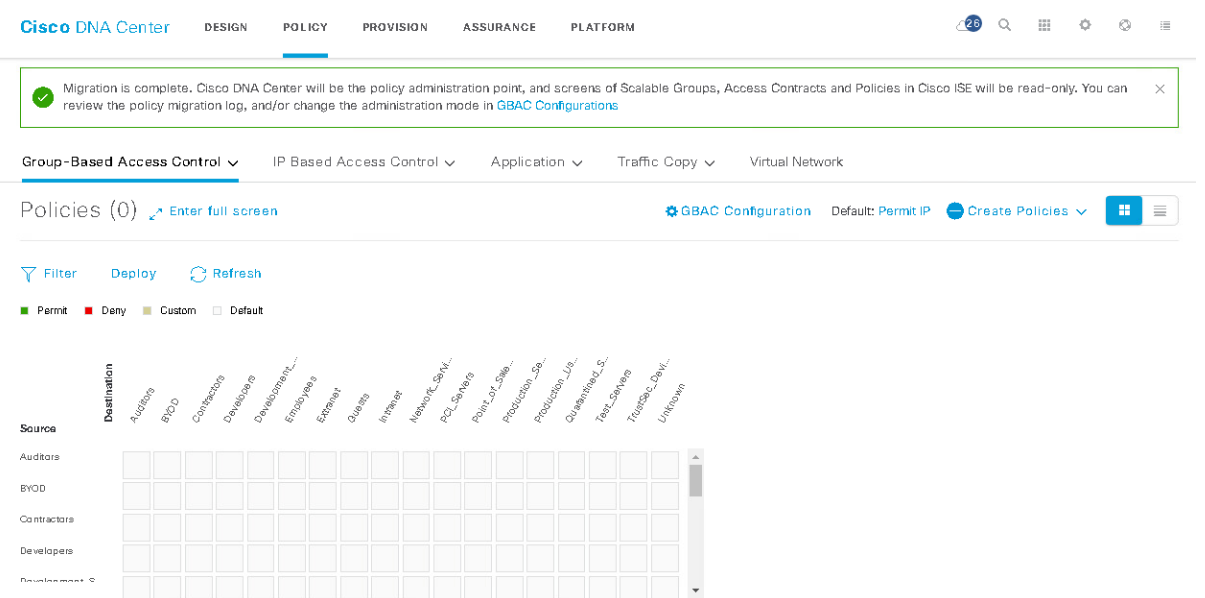
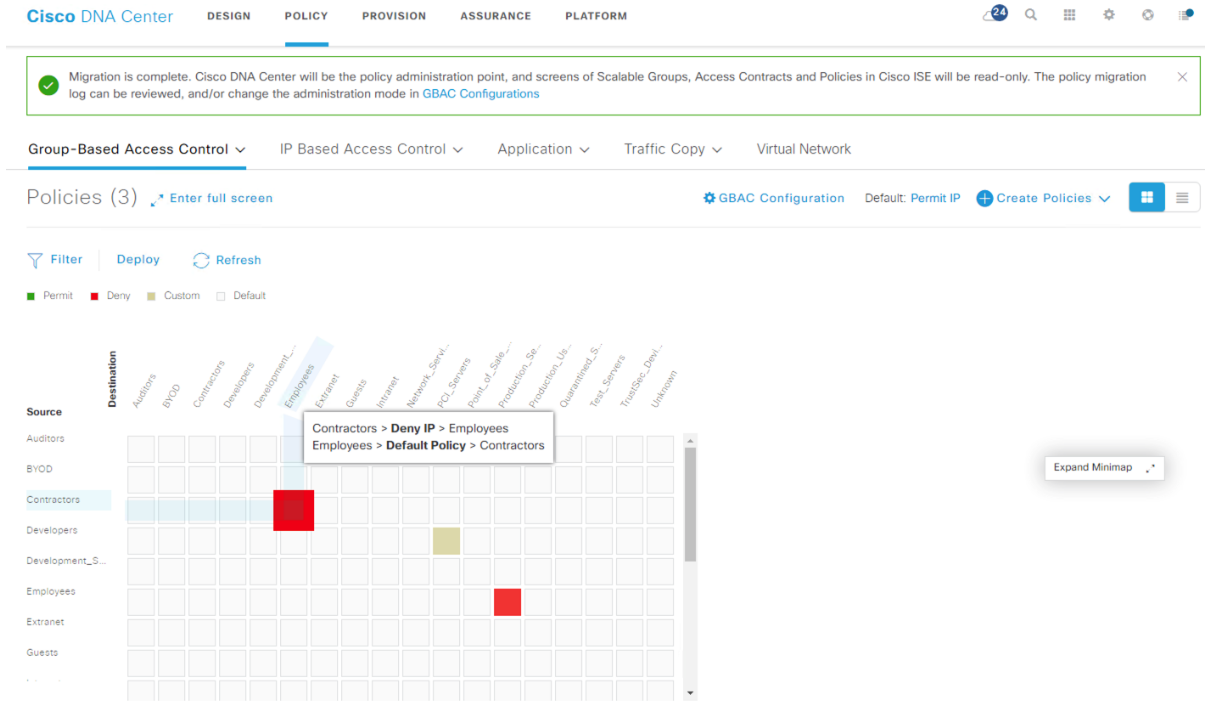
- Group-based access control policy
- Policy data from Cisco ISE must first be migrated to Cisco DNA Center
- Policy data includes SGTs, SGACLs, and the TrustSec policy matrix
- Once the policy data is migrated to Cisco DNA Center, it is visible in read-only mode on Cisco ISE
Scalable Group Tags
SGTs are 16-bit tags that are assigned to the users or endpoints connecting to the network. Each SGT is identified by a unique value. The SGT to which an endpoint belongs can be assigned statically or dynamically, and the SGT can be used as a classifier in the network policies.
SGTs are part of Cisco TrustSec and are defined in Cisco DNA Center as shown in the image below, but they reside in Cisco ISE
These are the main benefits of SGT-based policies compared to traditional IP-based policies:
- Logical grouping of users and endpoints regardless of IP and physical location
- Enabled endpoint roaming across the campus with the policy intact
- Groups can be assigned either dynamically or statically
Security Group Access Control Lists
Security group access control lists (SGACLs) are permissions that will be assigned after the Security Group Access (SGA) policy evaluation. SGACLs restrict the operations that a user can perform based on the role of the user instead of the IP address or subnet mask alone.
These are the key consideration regarding SGACLs:
- SGACLs are IP-agnostic access control lists based on SGTs.
- You create SGACLs within Cisco DNA Center as access contracts for group-based access control.
- Cisco ISE is required to deploy SGACLs.
Access contracts display the default and configured SGACLs, along with rule count and policy references.
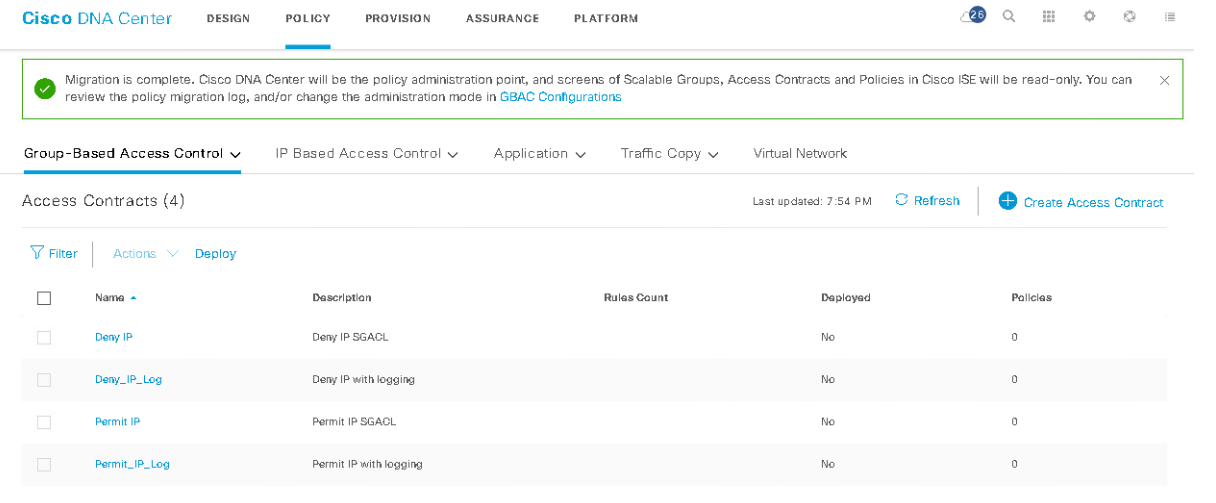
The Access contracts are assigned to a combination of source and destination SGT in a specific direction within the Cisco TrustSec policy matrix.
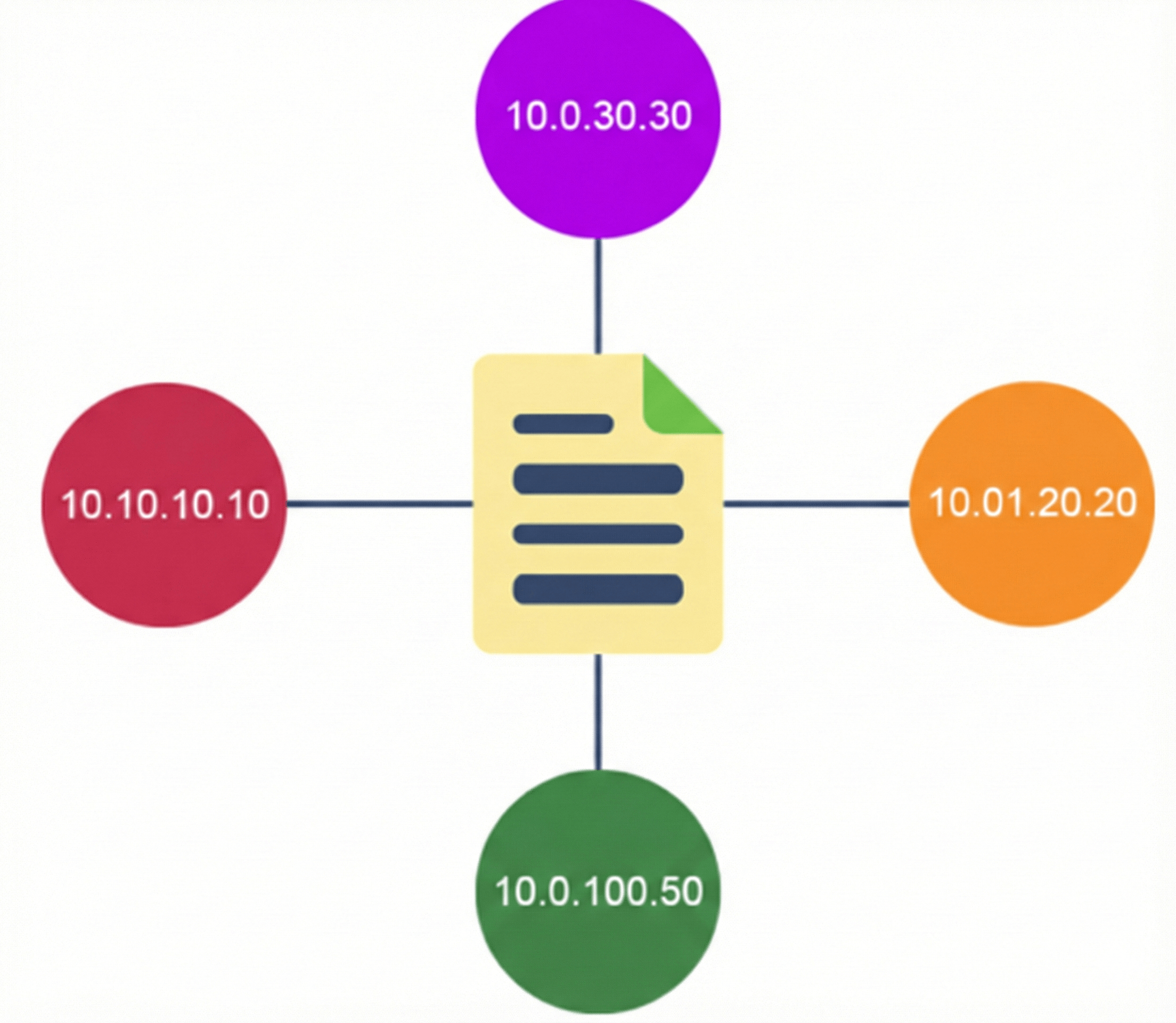
IP-Based Access Control
An IP-based access control policy controls the traffic going into and coming out of a Cisco device in the same way that an access control list (ACL) does. As with an ACL, an IP-based access control policy contains lists of permit and deny conditions that are applied to traffic flows based on various criteria, including protocol type, source IP address, destination IP address, or destination port number.
IP-based access control policies can be used to filter traffic for various purposes, including security, monitoring, route selection, and network address translation.
An IP-based access control policy has two main components:
- IP Network Groups: IP network groups comprise IP subnets that share the same access control requirements. These groups can be defined only in Cisco DNA Center. An IP network group may have as few as one IP subnet in it.
- Access Contract: An access contract is a common building block that is used in both IP-based and group-based access control policies. The access contract defines the rules that make up the access control policies. These rules specify the actions (permit or deny) performed when traffic matches a specific port or protocol, as well as the implicit actions (permit or deny) performed when no other rules match.
IP-based access control allows provisioning of IP access control policies in non-fabric wireless networks.





LEAVE A COMMENT
Please login here to comment.