EMAIL SUPPORT
dclessons@dclessons.comLOCATION
USCampus Wireless Design Consideration
Wireless Design Considerations: Below are the basic parameters that must be kept in mind, in order to design the campus wireless network.
High Availability:
High-Available wireless network ensure 24*7 network and application access over Wireless infrastructure. Below are some HA methods discussed for Wireless Infrastructure.
- High-Availability SSO
- N+1 HA
- WLAN Controller Link aggregation.
High-Availability SSO:
The two basic features that ensures the HA SSO are access-point stateful switchover and client stateful switchover which every Cisco AireOS supports. IF we are using this SSO option, and the time of controller recovery due to disruption reduces to sub-seconds. In this method whatever configuration and software upgrade is done on primary WLAN controller, they are automatically synchronized to standby controller.
N+1 High Availability :
This solution is used to provide redundancy for WLAN controllers at single site or for those sites are geographically remote located with lower cost of deployment.
Those site have Flex-Connect type connectivity. In order to provide high availability across DC for remote branches. In this one single WLC is used as backup to provide redundancy for multiple primary controllers. HA SSO is not supported in N+1 HA mode.
In N+1 mode, WLAN controller are independent of each other and they actually don’t share any configuration or IP address on any of their interfaces. Each WLC are managed separately and can be on different hardware and can be deployed in different DC across WAN links.
It is always advisable to use same WLC software versions on Primary and standby WLC in N+1 mode, in order to reduce down time as the APs establish CAPWAP sessions to backup controllers. APs can be configured with Priority and APs with Higher priority will first connect to primary controllers. When in case of primary goes down and then come UP, all APs will fall back from backup WLC to primary WLC automatically, if AP fallback option is enabled.
WLAN Controller Link Aggregation:
In this mode, multiple distribution systems ports are bundled when LAG is enabled to make it single logical high speed interface. If nay controller ports fails, traffic is automatically migrated to one of other ports as along as single ports in bundled interface is working.
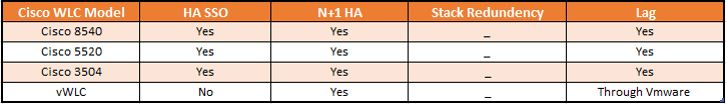
Below are the High-Availability Feature support of WLCs.
Multicast Consideration:
When WLC is configured as Multicast-multicast mode , then Campus WLAN will supports multicast traffic and in this WLC uses a multicast IP address to provide efficient communication for multicast streams to AP that have wireless users subscribed for that multicast group.
This mode is supported on Cisco 3500, 5500, 8500 WLC controllers.
IF there are remote site with Flex connect solution in local switching mode, they can also receive the multicast stream and use multicast based application.
Guest Wireless:
An Enterprise require Guest wireless to provide following functions to their guest and has following functionality.
- It Provides Internet access to guest via OPEN SSID with web authentication access control
- It helps in creating temporary authentication credentials for each guest required guest access
- It keeps Guest traffic separate from regular enterprise network traffic
- It also supports centralized and Cisco FlexConnect design models.
Below Figure correctly describes the Wireless Architecture overview of any enterprise .
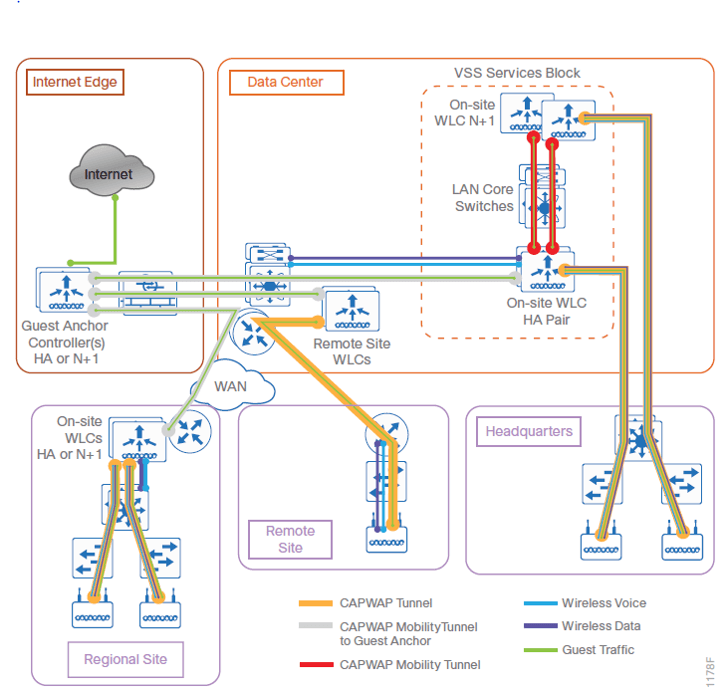
In some scenarios, a shared pair of controller is used for guest purpose and as well as Enterprise wireless access. In this case separate VLANs are created on distribution switch in order to logically segment both traffic, for Guest Network L2 VLAN is configured on distribution switch and is extended to DMZ where it terminates to DM FW where its Layer 3 SVI is configured and is used as Layer 3 SVI gateway for Guest network.
IF there is not shared environment, then use Cisco 5500, or Cisco 3500 WLC controller as dedicated controller, one pair is connected in DMZ and guest traffic from every controller in organization is tunneled to this controller.
In both Shared and dedicated guest wireless infrastructure design models, Internet Firewall restrict access from guest network. In most of the organization, Guest access to internet is only provided when user is authenticated.
Below are the multiple ways of authenticating guests on WLAN.
Local WebAuth: When guest want to access to guest network, its Web session is redirected to a web-portal containing login screen by guest wireless controller and this web portal is also provided by guest WLC only. The Guest credential is checked against local database within Guest WLC.
Central Web Authentication: When web session is created , Guest WLC redirect this session to external web-portal login screen, where he guest credentials are checked against external DB with level of authentication or authorization and accounting server. Cisco ISE is one of the best example which provides both external web portal and AAA server functionality.
CMX based Guest On-boarding: This type of implementation is used when organization wants to provide free internet access within their venue by collecting some information from customer or guest who visited the site. It can provide internet access by using their existing social media credentials.
This type of solution can be deployed by using Cisco CMX platform called as Mobility Engine. You can deploy Cisco Enterprise Mobility Services platform along with CMX in order to provide access via web-browser or by mobile app deployed in mobile.
Cisco OfficeExtend:
If the solution requires to create Home based office that will provide access to business services, Cisco OfficeExtend solution to be used.





LEAVE A COMMENT
Please login here to comment.