EMAIL SUPPORT
dclessons@dclessons.comLOCATION
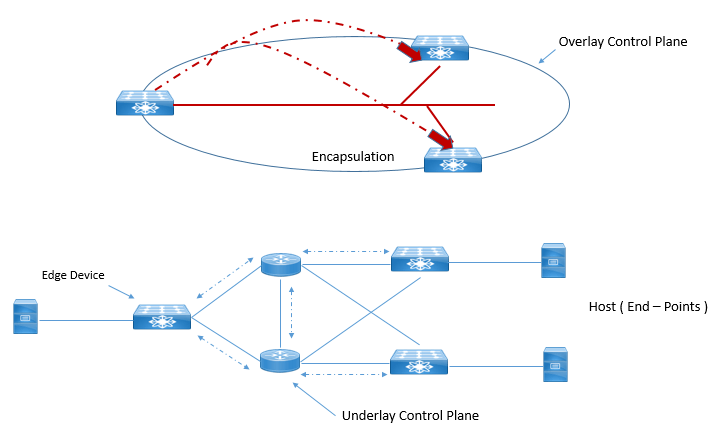
USCisco SD-Access network Layer consists of two sublayers that is network underlay and network overlay.
Let’s discuss one by one.
SD-Access Control Plane and Data Plane nut shell figure is given below
SD-Access Network Underlay:
This Underlay consists of Routers, Switches, and WLC, along with all combination of traditional routing protocols required to provide IP connectivity between each other , which further eliminates the requirement of STP , VTP , HSRP, VRRP etc. And On the top of it running a logical fabric topology builds functionality like multi-pathing, Optimized Convergence, Simplifies deployment & Troubleshooting.
Cisco DNA Center Automates the LAN which automatically discover, Provision, and deploy network devices. Once devices are discovered, the automated underlay provisioning leverages Plug & Play to configure Routing Protocols and further provides IP address Configuration.
Thera are two different models of network underlay supported.
Custom underlay: Existing Network or network which has been configured and managed manually with CLI or API without use of DNA Center.
Automated Underlay: Is the Underlay that is managed, orchestrated by DNA Central with full provisioning of all physical and logical interfaces address configuration, Control Protocols configuration, address configuration to provide full IP reachability between all fabrics enabled network devices, DNA, ISE etc.
In this you only have to provide necessary IP address to allow the IP reachability to the external network, rest all other aspect of network underlay and fabric overlay is fully automated.
SD-Access Fabric Overlay:
It is the logical, virtualized topology which are built on the top of underlay network. SD-Access Overlay has three main building blocks:
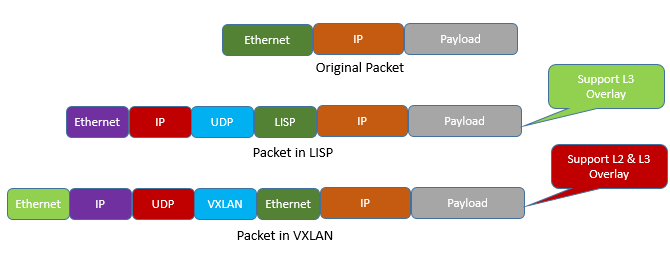
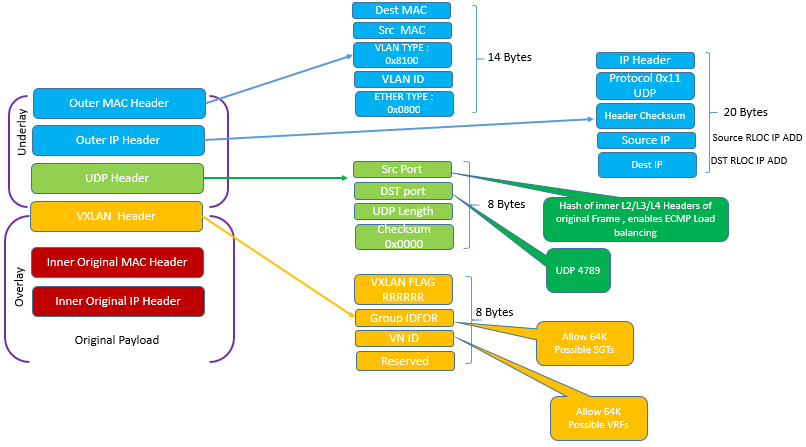
Fabric data Plane: Using VXLAN Protocols to send and receive data packet between source & Destination with Group Policy Option (GPO). VXLAN encapsulation is IP/UDP based and is used as Data plane over LISP because it includes Layer 2 header and also have option to include VNID and Group Segment ID. It also provides advantage for both layer 2 and Layer 3 virtual Overlays.
In SD-Access enhancement in original VXLAN is done to include Security Groups Tags (SGT), Group policy option.
Below Figure shows the fabric data plane based on VXLAN
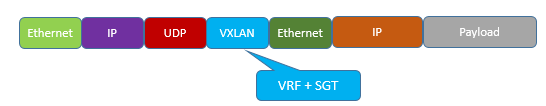
Below figure also shows how VXLAN – GPO header is used in SD-Access.
Fabric Control Plane: Logical mapping and resolving of users and devices with the help of LISP protocol. Fabric Control plane uses LISP technology , which every router uses in SD-Access fabric to share the all possible end host IP learned by it to Centralized Mapping DB located on MAP server or MAP resolver.
Cisco SD-Access has done lots of enhancement in original LISP specification including distributed Any Cast gateway, Virtual Network (VN) Extranet, Fabric Wireless
Fabric Policy Plane: Business Intent is translated to Network Policy using SGT (Scalable group Tags) and Group-based policies.
For fabric Policy plane, Cisco trustSec along with SGT and SGT Exchange Protocols (SXP) provides logical group based policy creation and enforcement by separating actual end point “identity “from its actual network IP address using a new ID called as SGT.
SGT is 16 bit tag ID which is separate from network address, which allow users to create network policies based on SGT only. When SGT and VN are combined together, a two-level hierarchical policy model is created.
The use of this technology has following advantages:
- Support for both VRF or VN based network
- Group based segmentation policy for wired and wireless
- Ability to provide policy construct over legacy or Non Cisco network
Below figure shows new VXLAN-GPO encapsulation that carries SGT and VNID.





LEAVE A COMMENT
Please login here to comment.