EMAIL SUPPORT
dclessons@dclessons.comLOCATION
USVLAN and VXLAN Mapping
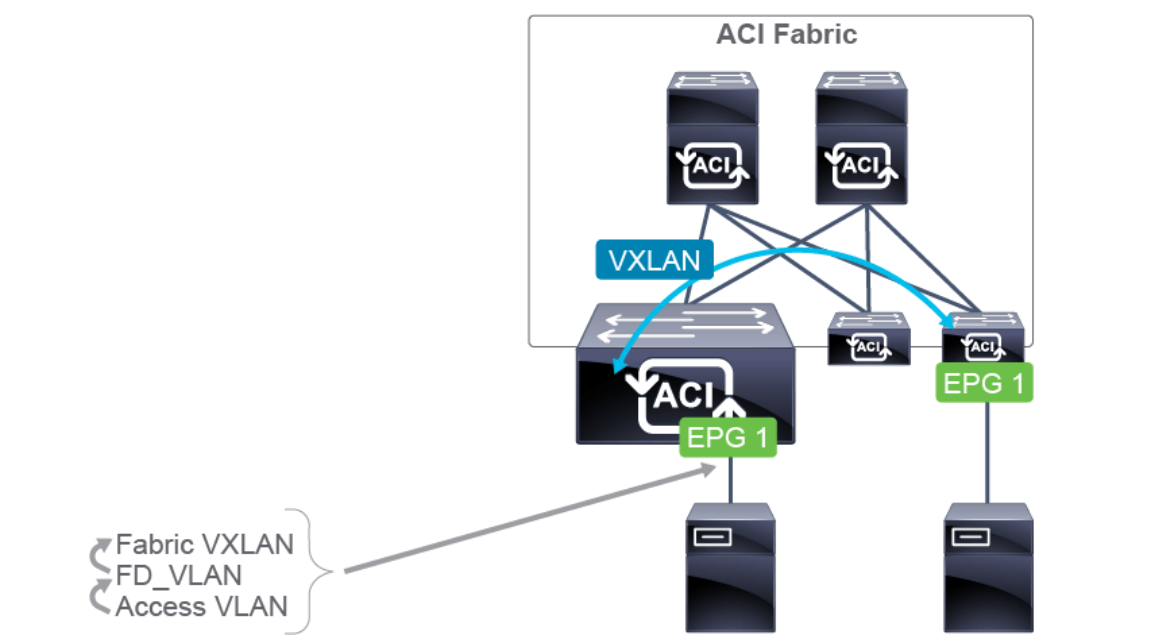
Endpoints connected to Cisco ACI leaf switches continue to use VLANs the same way they always have—traffic is either untagged (native) or tagged with 802.1Q VLANs. In Cisco ACI, a VLAN is simply an identifier used to classify endpoints into an Endpoint Group (EPG). The leaf switches then map these VLANs into VXLANs so traffic can be carried across the fabric. Instead of VLANs, the bridge domain represents the Layer 2 domain in ACI.
Internally, Cisco ACI uses several VLAN and VXLAN identifiers for different functions, such as forwarding STP BPDUs or handling broadcast, unknown unicast, and multicast (BUM) traffic. Knowing how these identifiers are used is important for integrating with traditional switched networks and for troubleshooting Layer 2 connectivity.
For example:
- Access Encapsulation VLAN (ACC_ENCAP): This is the VLAN used for traffic between the endpoint and the leaf port.
- FD_VLAN: This is a locally significant VLAN on the leaf switch, assigned to the configured access encapsulation VLAN in the EPG. It is then mapped to a VXLAN ID (VNID).
The Cisco ACI fabric uses different VLAN and VXLAN classes to handle traffic internally:
VLAN Classes
- Access Encap VLAN: Configured from a VLAN pool and enabled for the EPG on the port where the endpoint connects. These VLANs are not stored in the VLAN database and are not used for MAC learning. Instead, they classify traffic into security groups (EPGs).
- Bridge Domain (BD_VLAN): A locally significant VLAN on each leaf switch, assigned to a bridge domain. It maps Layer 2 traffic to the bridge domain’s VNID, which is consistent across all leaf switches for that BD. Broadcast, multicast, and unknown unicast traffic is sent through the BD VXLAN using multicast.
- Flood Domain (FD_VLAN): A locally significant VLAN assigned to each access encapsulation VLAN in an EPG. A bridge domain usually has multiple access VLANs, each with its own FD_VLAN. FD_VLANs are mapped to VNIDs, which must be consistent across all leaf switches where that EPG is present. MAC addresses are learned on these VLANs.
BD_VLAN and FD_VLAN are types of PI-VLANs (Platform-Independent VLANs). They act as an intermediate layer between access VLANs and VXLANs. This was necessary on older ACI hardware (Generation 1) that used Broadcom T2 ASICs, which did not support VXLAN. On those switches, access VLANs were converted into hardware VLANs to store Layer 2 information like MAC addresses. PI-VLANs allowed communication between Cisco ASICs and Broadcom ASICs. Newer hardware (Generation 2 and above) maps access VLANs directly to PI-VLANs without this extra step.
VXLAN Classes
- FD VNID: Matches the FD_VLAN. Used to forward traffic to all interfaces in the same FD_VLAN. By default, this is used for BPDUs.
- BD VNID: Matches the BD_VLAN. Used to forward all Layer 2 traffic (except BPDUs), including flooding, across the fabric to interfaces in the same bridge domain.
- VRF VNID: Used to forward routed traffic between two bridge domains.
VLAN and VXLAN Mapping: Same EPG and Bridge Domain
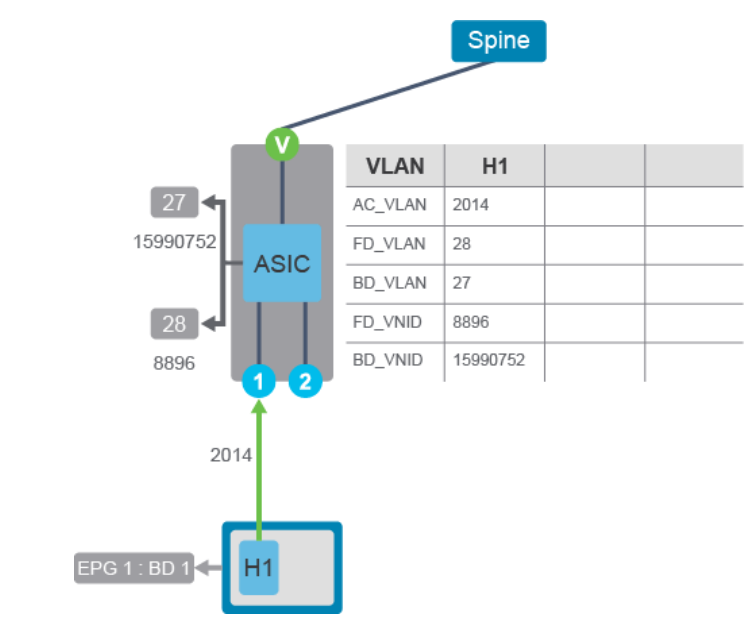
The communication between endpoints in a Cisco ACI fabric and VLAN to VXLAN mapping depends on the configured EPGs and bridge domain. The following example shows the VLAN to VXLAN mapping, when the endpoints (H1, H2, and H3) are configured under the same EPG and bridge domain (EPG 1 and BD 1), including the same VLAN access encapsulation. This figure shows the H1 connection.
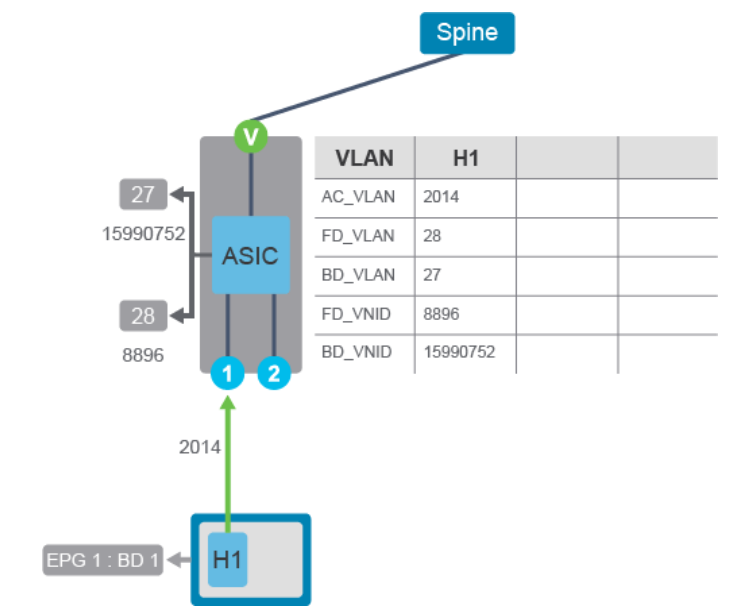
The following applies to the endpoint H1:
- Access VLAN (ID 2014) enters the leaf from the outside, containing the Ethernet frame from H1.
- H1 MAC address is mapped to the FD_VLAN (ID 28), with the associated VNID, which is 8896.
- H1 also gets associated into the BD_VLAN (ID 27) and BD_VNID, which is 15990752.
This figure also shows the H2 connection, which is connected on the same leaf switch as H1.
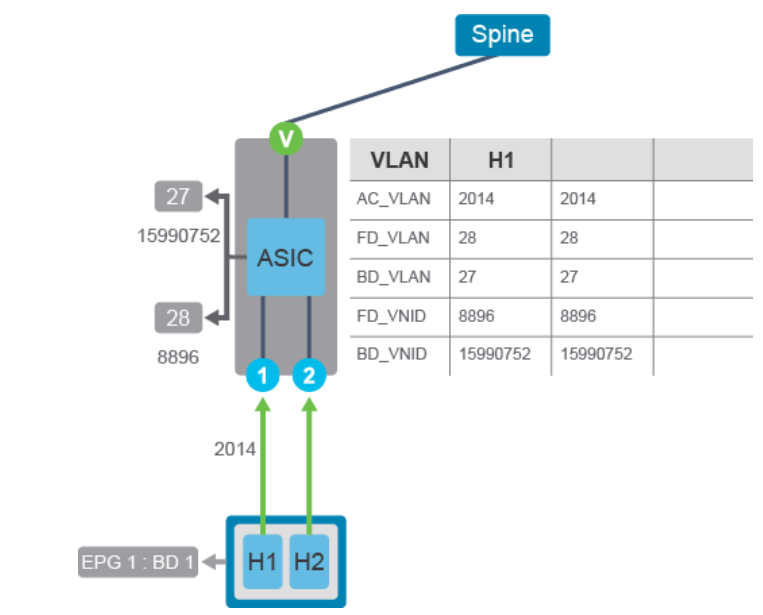
The following applies to the endpoint H2:
- Access VLAN (ID 2014) enters the leaf from the outside, containing the Ethernet frame from H2.
- H2 MAC address is mapped to the FD_VLAN, with ID 28 (same as H1), and with the associated VNID, which is 8896 (same as H1).
- H2 also gets associated into the BD_VLAN and VNID, which is ID 27 and 15990752 respectively (same as H1).
This figure shows the H3 connection, which is connected on different leaf switch than H1 and H2.
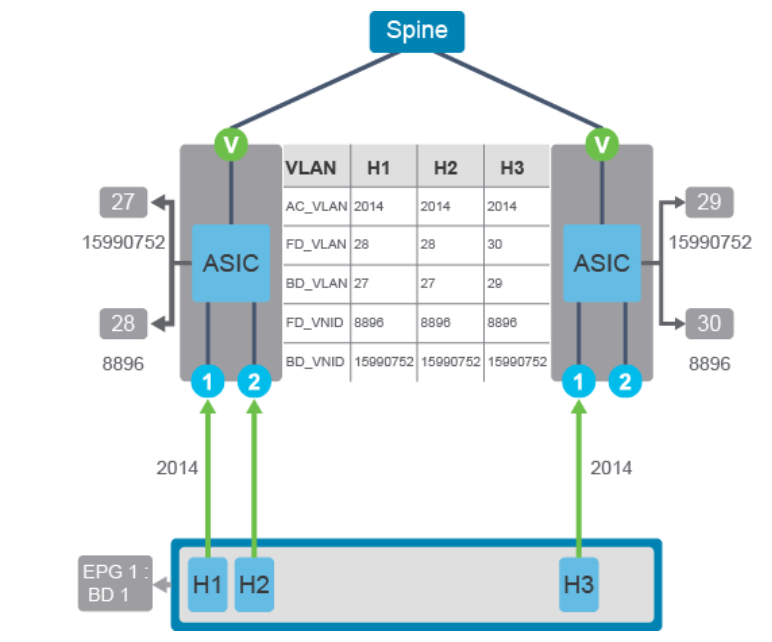
The following applies to the endpoint H3:
- Access VLAN (ID 2014) enters the leaf from the outside, containing the Ethernet frame from H3.
- H3 MAC address is mapped to the FD_VLAN, with ID 30 (leaf locally significant, and therefore, different than H1 and H2), and with the associated VNID, which is 8896 (same as H1 and H2).
- H3 also gets associated into the BD_VLAN, with ID 29 (leaf locally significant, and therefore, different than H1 and H2), and VNID, which is 15990752 (same as H1 and H2).
VLAN and VXLAN Mapping: Same EPG and Bridge Domain, Different Access/Encapsulation
This example depicts the VLAN to VXLAN mapping, when the endpoints (H1, H2, and H4) are configured under the same EPG and bridge domain (EPG 1 and BD 1), but in a different VLAN access encapsulation. H1 is in VLAN 2014, while H2 and H4 are in VLAN 2025. This figure shows the H1 connection.
The following applies to the endpoint H1:
- Access VLAN (ID 2025) enters the leaf from the outside, containing the Ethernet frame from H1.
- H1 MAC address is mapped to the FD_VLAN (ID 28), with the associated VNID, which is 8896.
- H1 also gets associated into the BD_VLAN (ID 27) and BD_VNID, which is 15990752.
This figure also shows the H2 connection, which is connected on the same leaf switch as H1, but in different access VLANs.
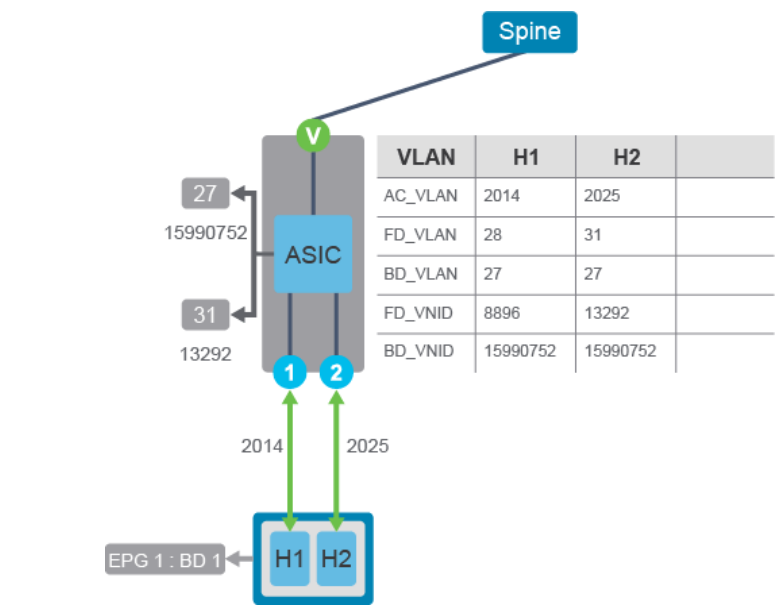
The following applies to the endpoint H2:
- Access VLAN (ID 2025) enters the leaf from the outside, containing the Ethernet frame from H2.
- H2 MAC address is mapped to the FD_VLAN, with ID 31 (different than H1), and with the associated VNID, which is 13292 (different than H1).
- H2 also gets associated into the BD_VLAN and VNID, which is ID 27 and 15990752 respectively (both same as H1).
H2 enters the fabric on a different access encapsulation, so it gets mapped to a different FD_VLAN and FD_VNID. The endpoints are still considered on the same Ethernet segment.





LEAVE A COMMENT
Please login here to comment.