EMAIL SUPPORT
dclessons@dclessons.comLOCATION
USHUB & Spoke Topology
HUB VNet acts as a Central Point of connectivity to many Spoke VNets. HUB can also be used as connectivity point to your On-Premises Network. The spoke Virtual network also peer with HUB network and can be used to isolate workloads.
Architecture:
Below Architecture defines the Azure HUB and Spoke Topology
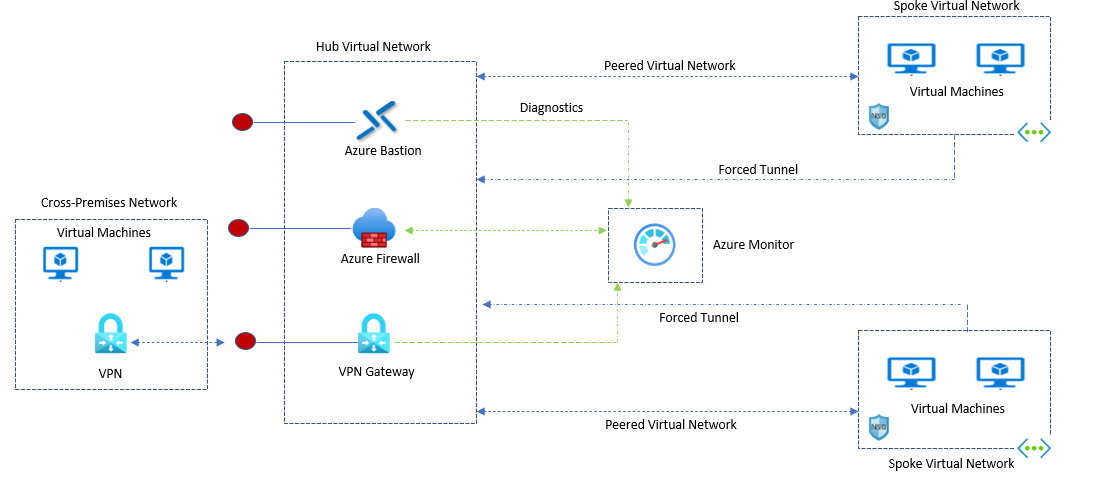
Now lets understands the workflow. Architecture defines the following aspects:
HUB Virtual Network: It is the central Point of connectivity to On-premises network, This HUB network is used to host services that can be consumed by different workloads hosted in the Spoke network.
Spoke Virtual Network: This network is used to isolate workloads in their own Virtual network, managed separately from another spoke. Each workload might include multiple tiers, with multiple subnets connected though Azure Load balancer.
Virtual Network Peering: Two VNets can be connected using a peering connection. Peering connection are non-transitive, Low latency connection between Virtual Network. Once Peered Virtual Networks exchange traffic by using Azure backbone.
Bastion Host: With Azure Bastion host, you can securely connect to Workload deployed inside an Azure Virtual Network and can access Virtual machine in peered Networks.
Azure Firewall: It is the managed Firewall as Service. The Firewall instance is placed in its own subnet.
VPN Virtual Network gateway or ExpressRoute Gateway: The Virtual Network gateway enables the Virtual network to connect to VPN device or ExpressRoute circuit, used for connectivity with your On-premises network.
VPN Device: A Device or Service that provides external connectivity to the On-premises Network. VPN device may be hardware device or a software solution such as Routing and Remote Access Service ( RRAS ) in windows Server 2012.
HUB and Spoke Architecture Use-case:
Below are some typical use-case related to this Architecture:
- Workload which are deployed in different environments (Dev, test, Prod) that require shared services like DNS, DHCP, IDS, NTP, AD DS. All Shared Service are placed in HUB virtual network, while each environment is deployed in spoke to maintain isolation.
- Workloads that do not require connectivity to each other but require access to shared services.
- Enterprise that requires central control over security like Firewall in HUB as DMZ and segregated management for workloads in each spoke.
Recommendation for HUB and Spoke Architecture
Below are some recommendations that can be taken into consideration while designing HUB and Spoke Architecture.





LEAVE A COMMENT
Please login here to comment.