EMAIL SUPPORT
dclessons@dclessons.comLOCATION
USLAB: Configure Site to Site VPN between AWS Cloud and your DC network.
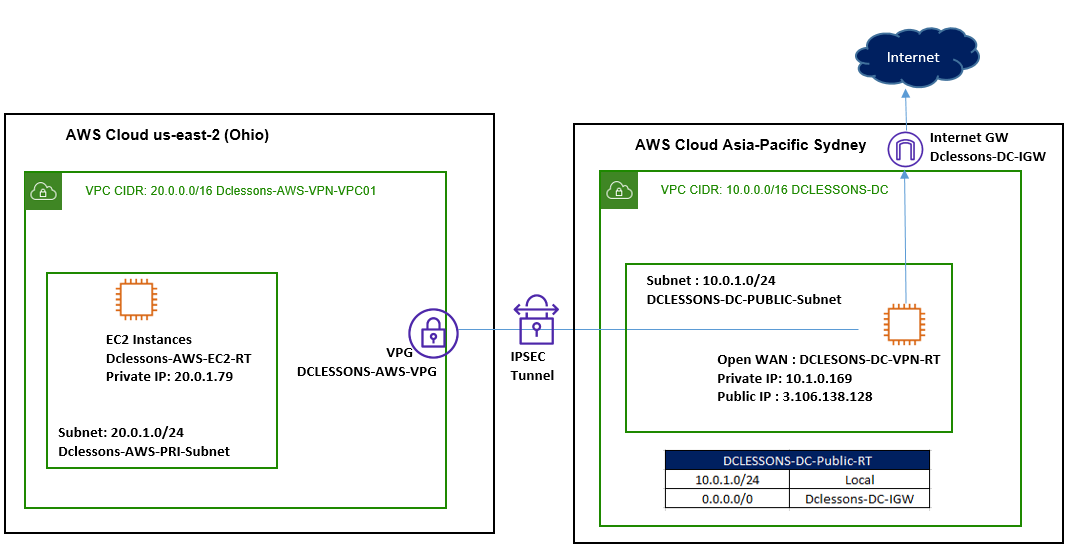
Topology:
Refer below figure for VPN Setup.
Task:
- Create a VPC DCLESSONS-DC in the Sydney Region. Create a Public subnet DCLESSONS-DC-PUBLIC-Subnet (10.0.1.0/24)
- Create and attach an Internet Gateway to VPC DCLESSONS-DC
- Create a Public Route Table DCLESSONS-DC-Public-RT and associate it with the subnet 10.0.1.0/24.
- Add the default Route 0.0.0.0/0 in the Route table DCLESSONS-DC-Public-RT
- Launch an EC2 instance in VPC DCLESSONS-DC
- Create a VPC Dclessons-AWS-VPN-VPC01 in Ohio Region. Create a Private subnet Dclessons-AWS-PRI-Subnet (20.0.1.0/24)
- Launch an EC2 instance in VPC Dclessons-AWS-VPN-VPC01
- Create a Customer Gateway in Ohio Region and Create a Virtual Private Gateway in same Region.
- Create a Site-to-Site VPN connection between both VPC
- Configure On-Premises Router DCLESSONS-DC-VPN-RT
- Test the connectivity between two Networks.
In this Lab scenario, since we don’t have a (remote/ on-premises) network we will be simulating a corporate network in AWS itself. We will be creating a VPC in the Sydney region and launch an EC2 instance with Openswan which will act as a Public Router of the on-premises network.
Solution:
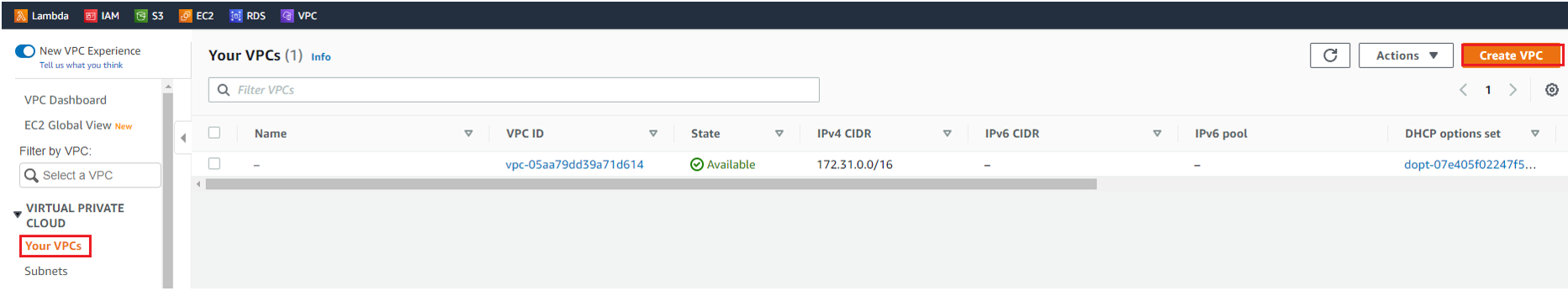
Go to AWS Services | VPC | Click Create VPC | Select Sydney Region.
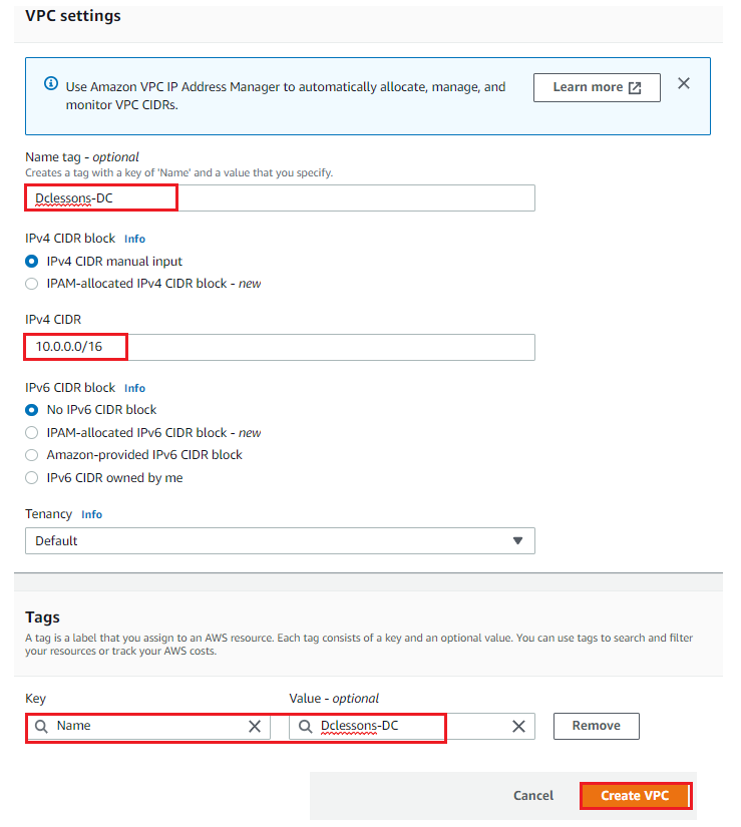
In VPN Setting | Name Dclessons-DC | CIDR: 10.0.0.0/16 | Tenancy: Default | Tags Name: Value: Dclessons-DC | Create VPC
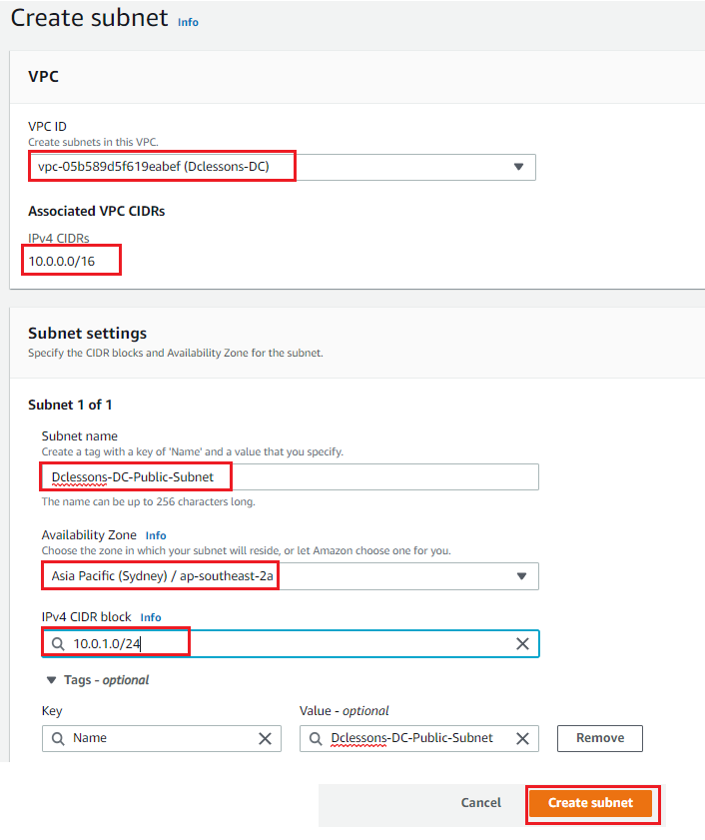
In Subnet Section | Click to Create Subnet | Select VPC ID : Dclessons-DC | Subnet name: Dclessons-DC-Public-Subnet | AZ : Sydney:ap-southeast-2a | Tags : Name: Value: Dclessons-DC-public-Subnet | Create Subnet
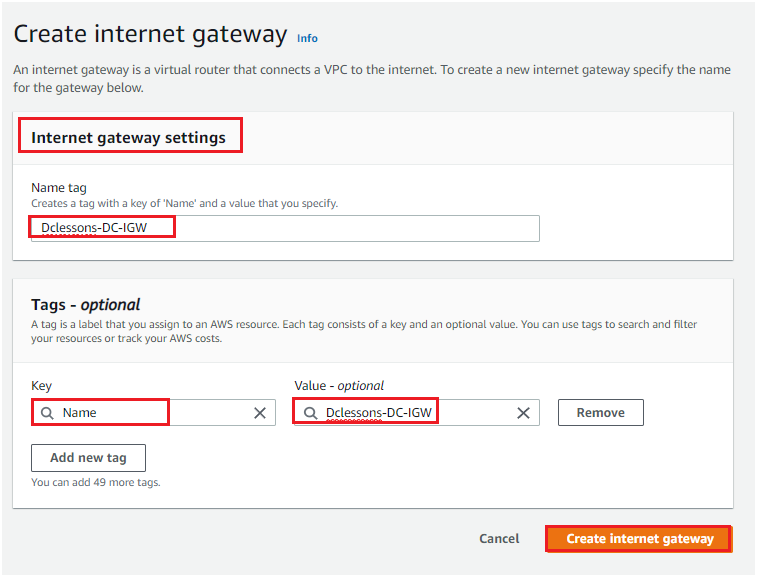
Select Internet Gateway | Click to Create Internet Gateway | In Internet Gateway Setting: Name: Dclessons-DC-IGW | Tag : Name: Value : Dclessons-DC-IGW | Click Create Internet gateway
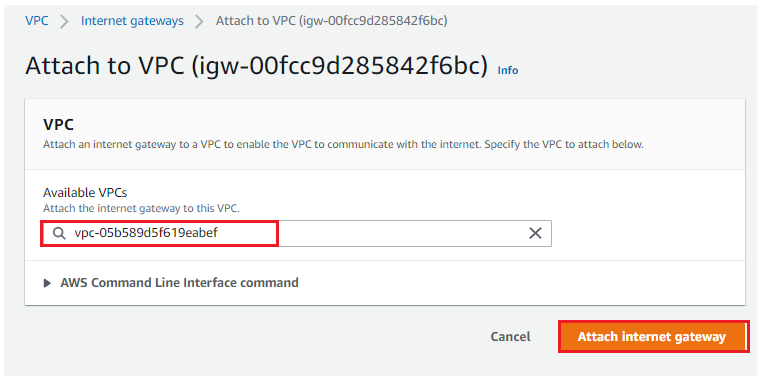
Now Select the Internet Gateway, which you have created and Select the VPC and click to Attach Internet Gateway
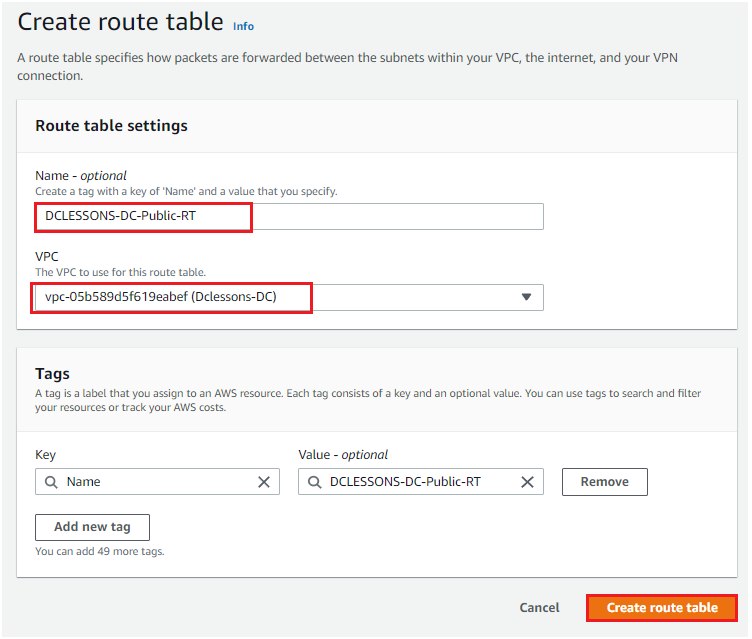
Select Route table | Click to Create Router table | Name: DCLESSONS-DC-Public-RT | Select VPC: Dclessons-DC | Click Create Route Table
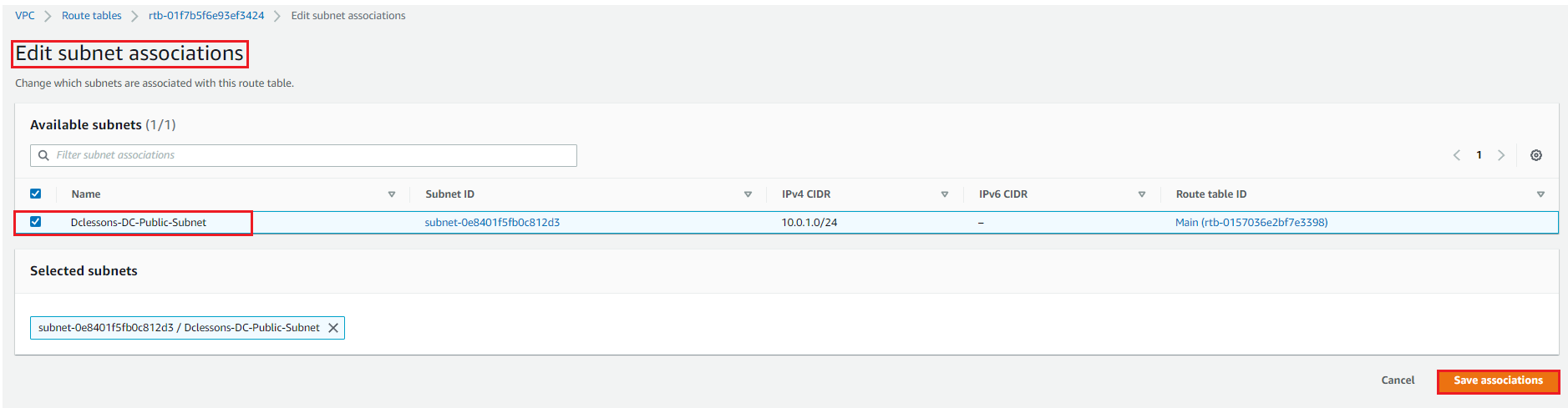
Select the RT and Edit Subnet Association | Select the Subnet Dclessons-DC-public-Subnet | Save Association
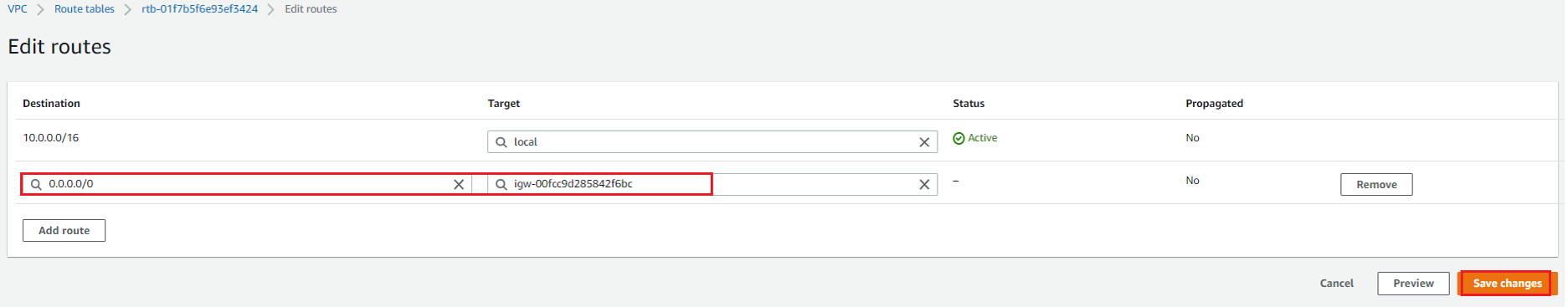
Click Routes | Edit Routes | add 0.0.0.0/0 with target Internet Gateway | Save Changes
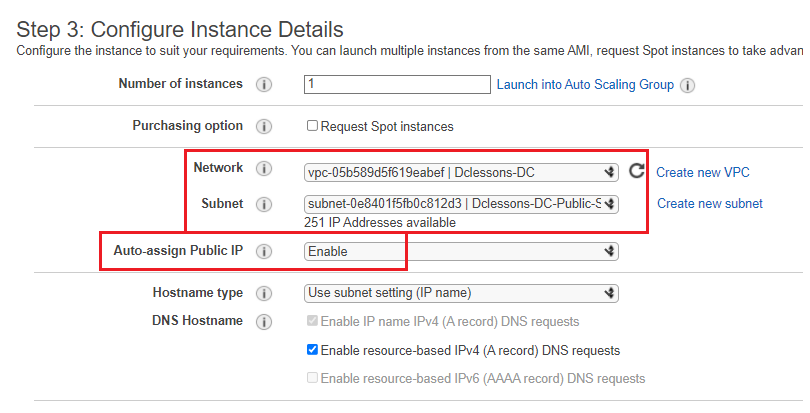
Go to AWS Services | EC2 | Click launch Instances | Select Amazon Linux AMI | t2.micro Instance Type | In Configure Instance Details section | Network : Dclessons-DC | Subnet: Dclessons-DC-Public-Subnet | Auto-Assign Public IP : Enable | Click Configure Storage
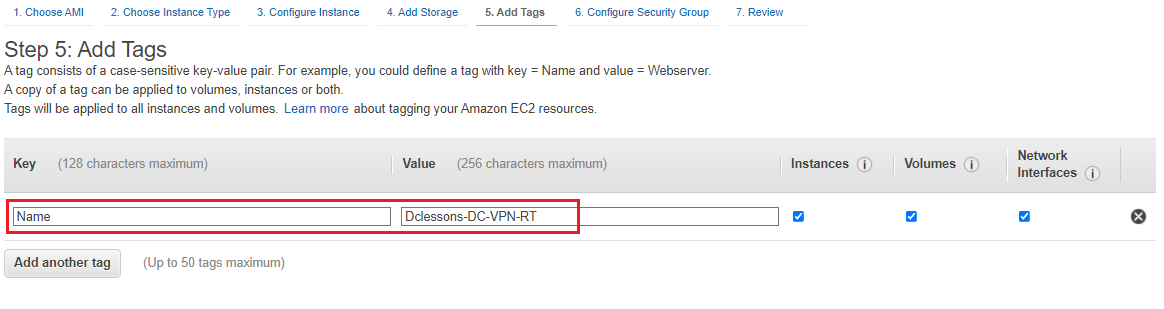
Click Next for storage section and in Tag Name: value: Dclessons-DC-VPN-RT |Click Configure Security Groups
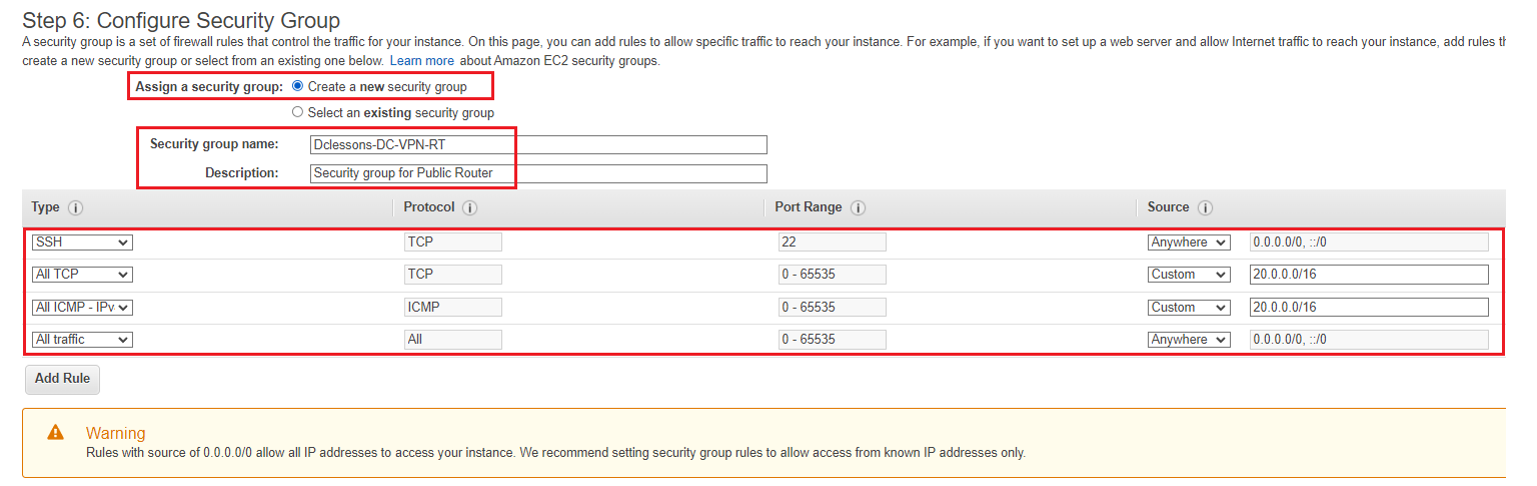
In Configure Security Group Section , Select Create a new Security group | Name: Dclessons-DC-VPN-RT and allow all protocols and Port as defined in below figure
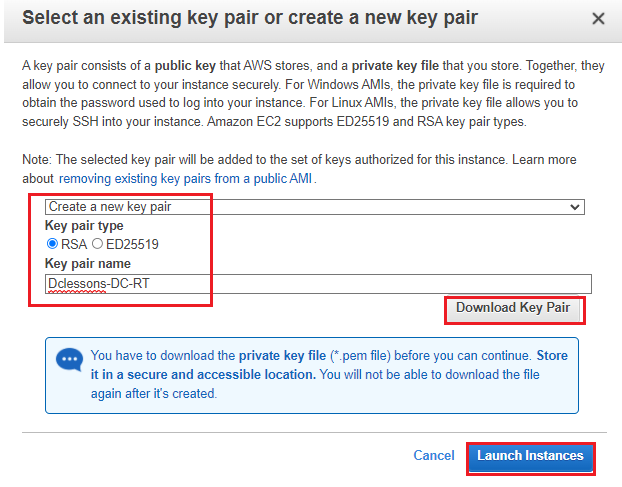
Click to create a new key pair for accessing this instance and shown in below figure
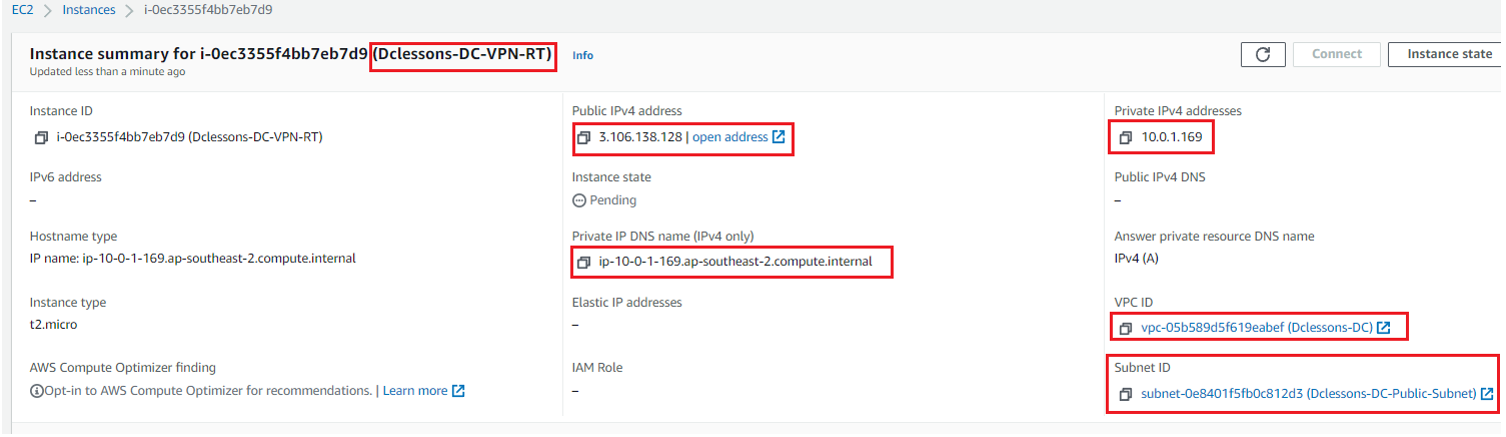
Now Once Instance is launched, it has public IP 3.106.138.128 with private IP 10.0.1.169
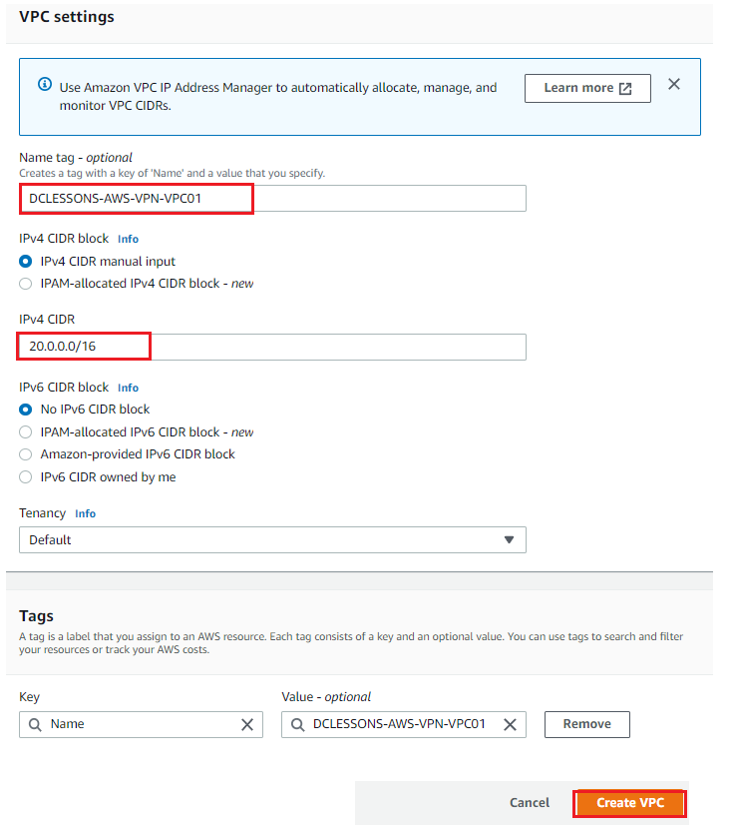
Now Let’s Create another VPC in Ohio region. Go to AWS Services | VPC | Create VPC
Name: DCLESSONS-AWS-VPN-VPC01 | IPv4 CIDR: 20.0.0.0/16 | Create VPC
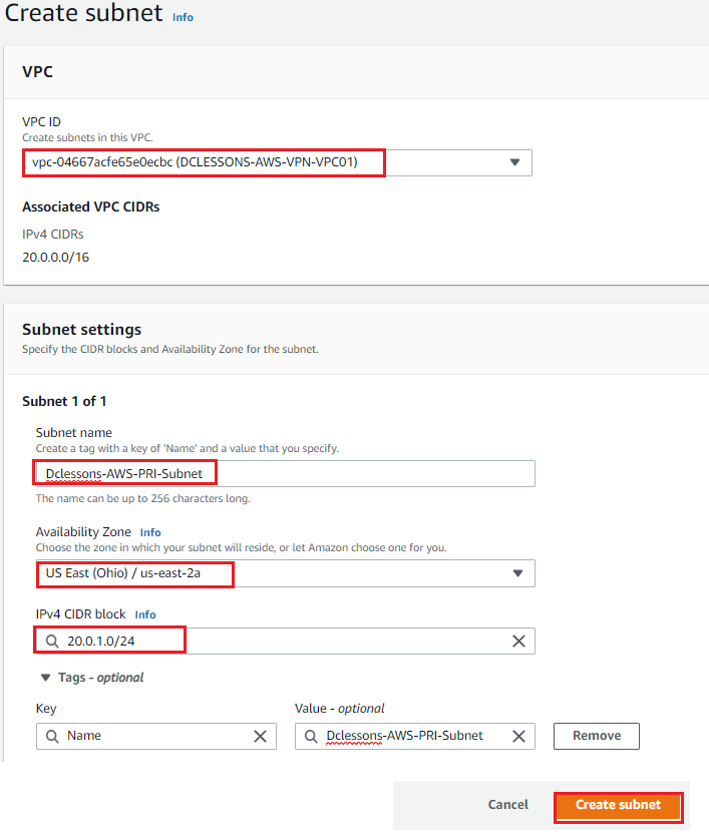
In Subnet Section | Click to create Subnet | Select VPC: DCLESSONS-AWS-VPN-VPC01 | Subnet Name: Dclessons-AWS-PRI-Subnet | AZ: Ohio/us-east-2a | IPv4 Block : 20.0.1.0/24 | Click to Create Subnet
Launch an EC2 instance and use the Configuration as given below in figures.





LEAVE A COMMENT
Please login here to comment.