EMAIL SUPPORT
dclessons@dclessons.comLOCATION
USRole based Access Control
When user is authenticated using its credential via Azure AD, an authorization needs to done for that user, which provides the access rights or privilege to access particular resources.
With the RBAC, we can implement the Authorization to access resources. RBAC feature is accessible using Azure portal, Azure CLI, Azure PowerShell and REST.
In RBAC, custom roles are not supported and RBAC is used to manage access to Azure Resources.
There are three main common RBAC roles in Azure and about 40 built-in roles in total.
- Owner: Access to all resources, also can delegate this rights to others.
- Contributor: Same as Owner But cannot delegate this rights to others.
- Reader: Can only view existing Azure resources, cannot create or delegate.
Each role has set of permission, and then each individual is added to that role. In Azure RBAC, each individual accounts can be assigned to multiple roles, which allows them to execute and perform many tasks.
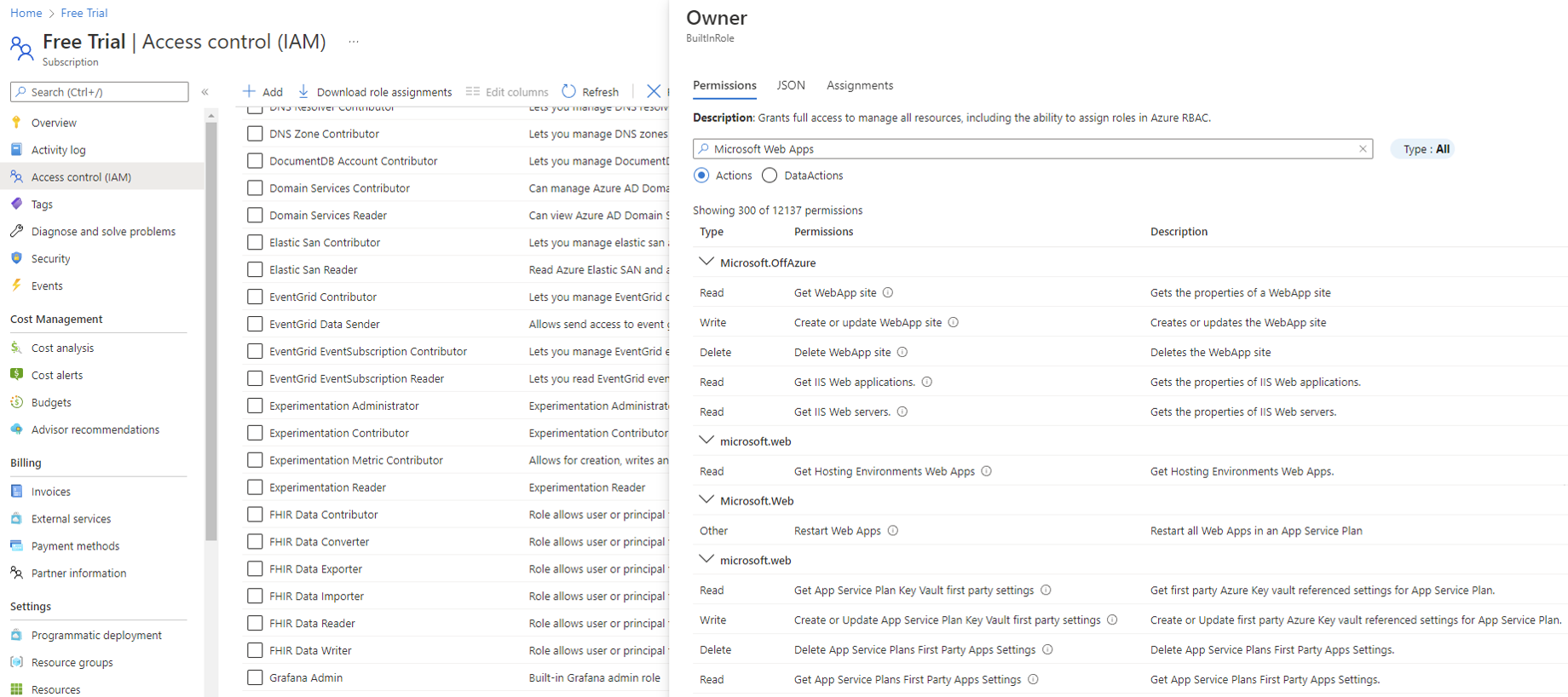
The Permission for the Owner RBAC role in Azure can be viewed in the portal by selecting Subscription, choosing an Azure subscription accessible to the signed-in-user, and then choosing access Control (IAM) | Roles | Owner | Permissions. Finally click the load more link a few times.
Now click to any one of the permission categories and you will see the access controls (Read, Write, Delete, and other) provided for the role.
Providing Permission to Resources
As we know, Azure Architecture has a scope hierarchy, like Management Group, Subscription, resource Group, Resources etc , At each level , we will find the Access Control (IAM) menu option or link which provides the interface for granting access.
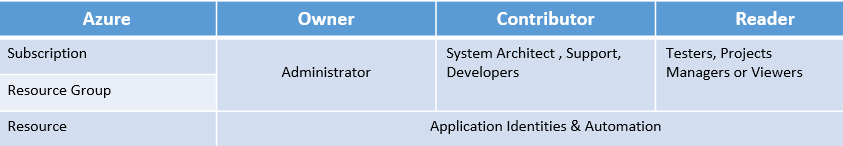
Below figure describes the best-practice approach to grant user access to Azure Resources via Roles and visualizes the most common roles (Owner, Contributor , reader ) mapped to Scope Hierarchy.
Controlling Permission to Resources
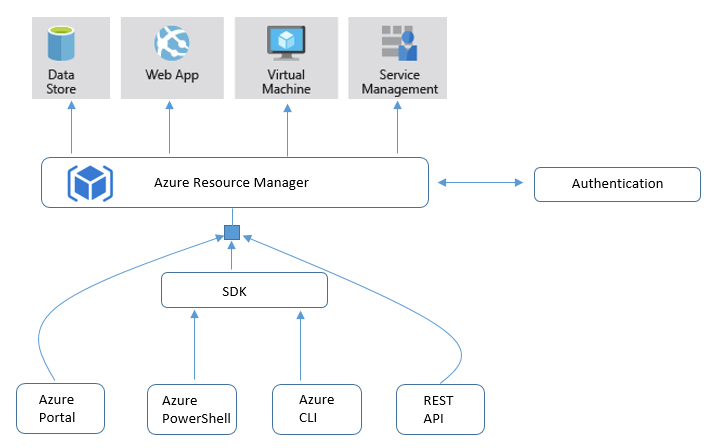
Permission to Access resources can be done by Implementing RBAC and also by using ARM (Azure resource manager). ARM is an API, which is used for auditing, tagging, controlling access to resources. ARM helps in logically structuring of an enterprise workloads and compute solutions. Due to which it is possible to implement access control on a resource , group of resource , or even all resources within a given subscription.
Below figure describes the Azure and resource manager relationship.
Hardware & Network Security
In real scenarios, Cloud Service provider mostly focuses on protecting their platform, and No Cloud Provider can know what vulnerabilities exists within your code or packages used by customer and its customer responsibility for all these security checks.
Azure provides few products and features that can improve the security level for customer of all kinds.
Microsoft trust Center:
This tool is used to gather security and compliance information.
Security Center :
It is an Azure Product , that helps in implementation and Maintenance of Security policies. It Analyze the Azure work load and find Vulnerabilities.
It is used for following purpose:
- Policy & Compliance :
- Resource & Security Hygiene
- Advance Cloud Defense
- Threat Protection





LEAVE A COMMENT
Please login here to comment.