EMAIL SUPPORT
dclessons@dclessons.comLOCATION
USMonitoring Azure Resources
why you want to monitor is an easy question to answer. You must know how the platform and how your applications running on the platform are behaving. Your objective is to meet the service level agreements (SLAs) you have guaranteed to your customers, partners, and/ or the business organization within your company.
In addition to meeting an SLA, you also should desire an IT solution that is both reliant and resilient. To achieve those objectives, focus your monitoring strategy on the following monitoring aspects:
- Availability/SLA monitoring
- Collecting, storing, and reporting
- Auditing
- Health monitoring
- Performance monitoring
- Security monitoring
- Usage monitoring
application availability is simply the amount of time the application is accessible for use. Calculating the availability of an application is achieved by using the following algorithm:
percent_availability = ((total_time - total_downtime) / total_time) * 100
Common values for percent_availability are, for example, 99.9%, 99.95%, 99.99%, and 99.999%
There are certainly tools and metrics that can help you track the availability metric.
The Azure portfolio offers the following services for collecting, storing, and reporting details about your workloads:
- Azure Monitor
- Log Analytics
- Application Insights
- Azure Data Explorer (ADX)
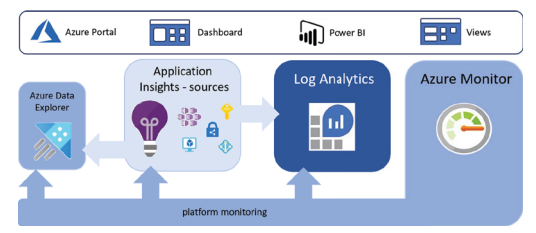
In Below figure , You can see that Azure Monitor is in place to monitor the products running on the Azure platform and feed that data into Log Analytics for reporting. As well, monitoring data can be fed directly into Azure Data Explorer (ADX) or into some custom logging source. Application Insights is a tool that is useful for capturing logs that are more application-specific, i.e., not platformspecific. This monitoring data can be fed into numerous repositories and analyzed from the portal where the information is graphically presented.
Logging can be configured to track and monitor Azure VMs, containers, security, Azure Active Directory, and subscriptions. Just about all Azure products and features have the capability to create logs and expose an interface to retrieve and analyze them.
Additionally, there are dashboards and views in Application Insights, Log Analytics, and ADX that allow you to customize the data to analyze and customize the presentation of it.
Now in Auditing , Being compliant with industry regulations and government privacy laws cannot be achieved without knowing what exists in your Azure footprint, what each resource does, and whether they are secure. There are some helpful tools in Security Center for auditing as well. In addition to Security Center, Azure Policy and Azure Blueprint are helpful in making sure your solutions remain compliant.
health monitoring. What exactly is health monitoring? If you have a bad piece of code that consumes an unnecessary amount of CPU or memory, then the compute can perform fewer computations over the same time frame when compared to the same process running a more optimal version of the code.
Bad, inefficient code can result in higher average costs since they consume more cloud resources. Health monitoring is generally constructed using colors. Green is when all is good, yellow is for partially good, and red is for not good.
In Performance , Key performance indicators (KPIs) are the indicators for performance Monitoring.
KPIs are the thresholds you set for your application in the context of, but not limited to,
- how fast an HTTPS response should take
- how fast a database query should take
- how long a ping between two servers should take
- how many concurrent connections is normal.
When any of those KPIs are breached, then alerts need to be sent and analysis done to find out what happened and implement a solution to keep it from happening again if it caused downtime. If it didn’t cause downtime or any disruption, then you should consider changing the KPIs so that it reflects “normal production activity.”
In context of Security Monitoring , Azure Security Center plays a vital role.
Security Center :
It is an Azure Product , that helps in implementation and Maintenance of Security policies. It Analyze the Azure work load and find Vulnerabilities.
It is used for following purpose:
- Policy & Compliance :
- Resource & Security Hygiene
- Advance Cloud Defense
- Threat Protection
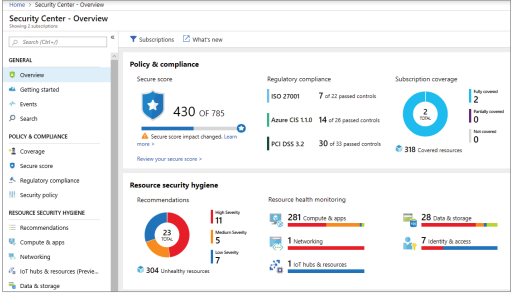
Below figure describes the Security center overview portal blade.
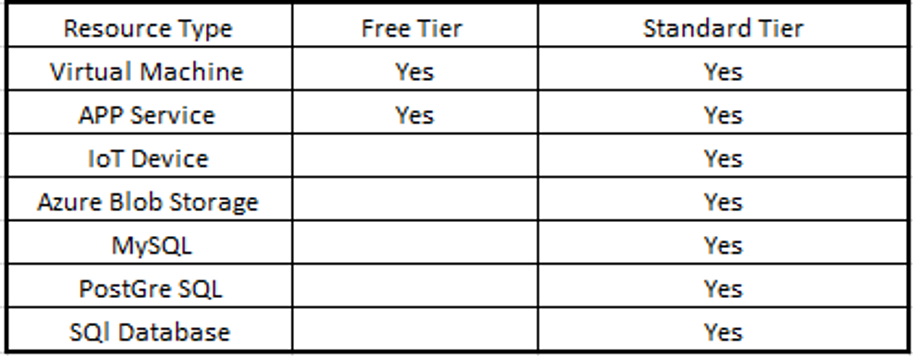
There are two tiers of Security Center: Free & Standard. Below figure describes what is supported in each tier.
Policy & Compliance: includes coverage of subscription, regulatory compliance , Secure Score feature ( enabling MFA, Enabling advance data security , enabling JIT network access ) all have an associated score , which provides overall score for all resources in the subscription as well as a breakdown per category such as compute , data storage , network and identity.
Resource security Hygiene provides overall list of security related recommendation by subscription as well as resource type. When we click the recommendation link, we will get list of all recommendation, the score received for implementing them, Number of resources by type that are impacted and their severity.
Below figure shows the Security Center recommendation






LEAVE A COMMENT
Please login here to comment.