EMAIL SUPPORT
dclessons@dclessons.comLOCATION
USCisco SD-Access Distributed Campus
Cisco SD-Access for Distributed Campus is a metro-area solution that connects multiple independent fabric sites together, while maintaining the security policy constructs (VRFs and SGTs) across these sites. Multi-site environments and deployments have been supported with Cisco SD-Access for some time, and at first, there was no automated and simplistic way to maintain policy between sites. At each site fabric border node, fabric packets were de-encapsulated into native IPs. Combined with SXP, policy could be carried between sites using native encapsulation. However, this policy configuration was manual, mandated use of SXP to extend policy between sites, and involved complex mappings of IP-to-SGT bindings within Cisco ISE.
With Cisco SD-Access for Distributed Campus, SXP is not required, the configurations are automated, and the complex mappings are simplified. This solution enables inter-site communication using consistent end-to-end automation and policy across the metro network.
Cisco SD-Access for Distributed Campus uses control plane signaling from the LISP protocol and keeps packets in the fabric VXLAN encapsulation between fabric sites. This maintains the macro and micro segmentation policy constructs of VRFs and SGTs, respectively, between fabric sites. The original Ethernet header of the packet is preserved to enable the Layer 2 overlay service of Cisco SD-Access wireless. The result is a network that is address-agnostic, as the policy is maintained through group membership.
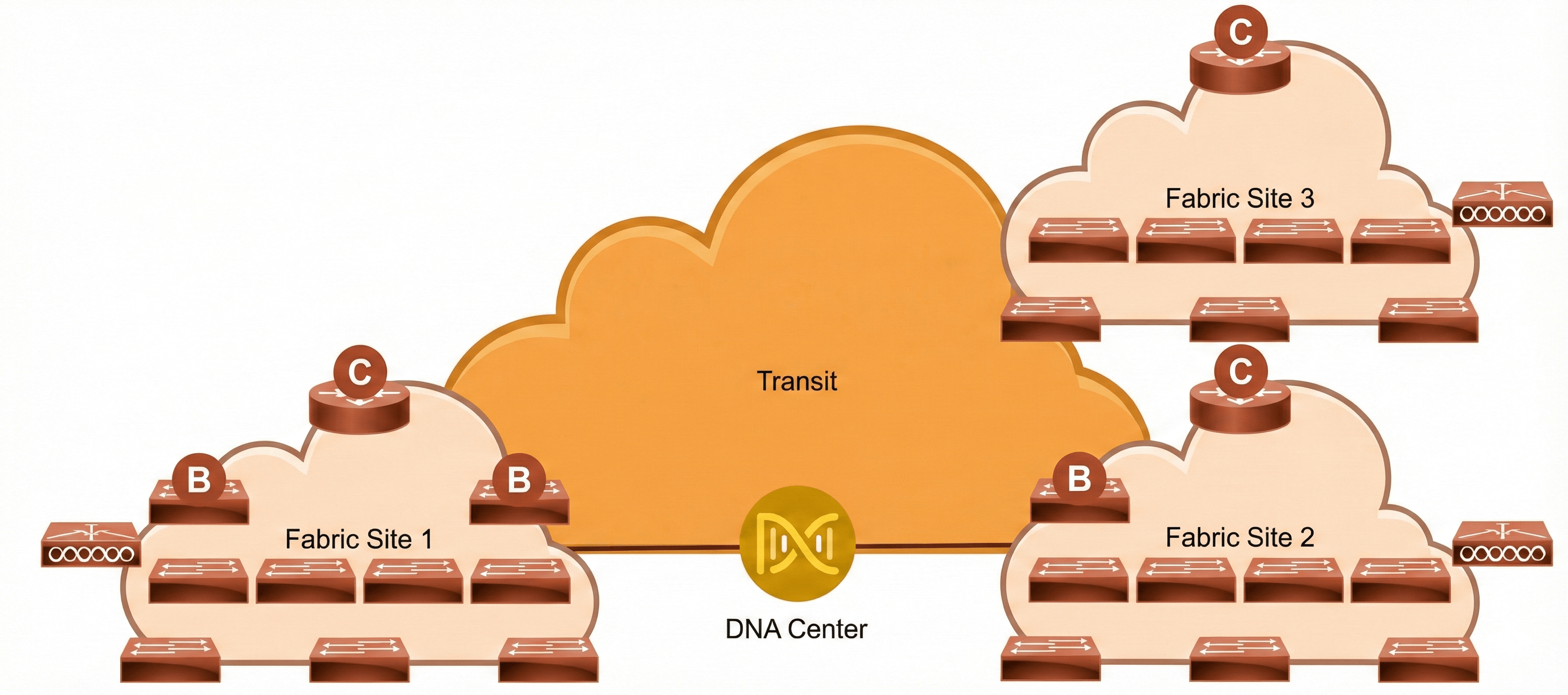
The core components enabling the Cisco SD-Access Distributed Campus solution are the Cisco SD-Access transit and the transit control plane nodes. Both are new architectural constructs introduced with this solution. The Cisco SD-Access transit is simply the physical metro-area connection between fabric sites in the same city, metropolitan area, or between buildings in a large enterprise campus.
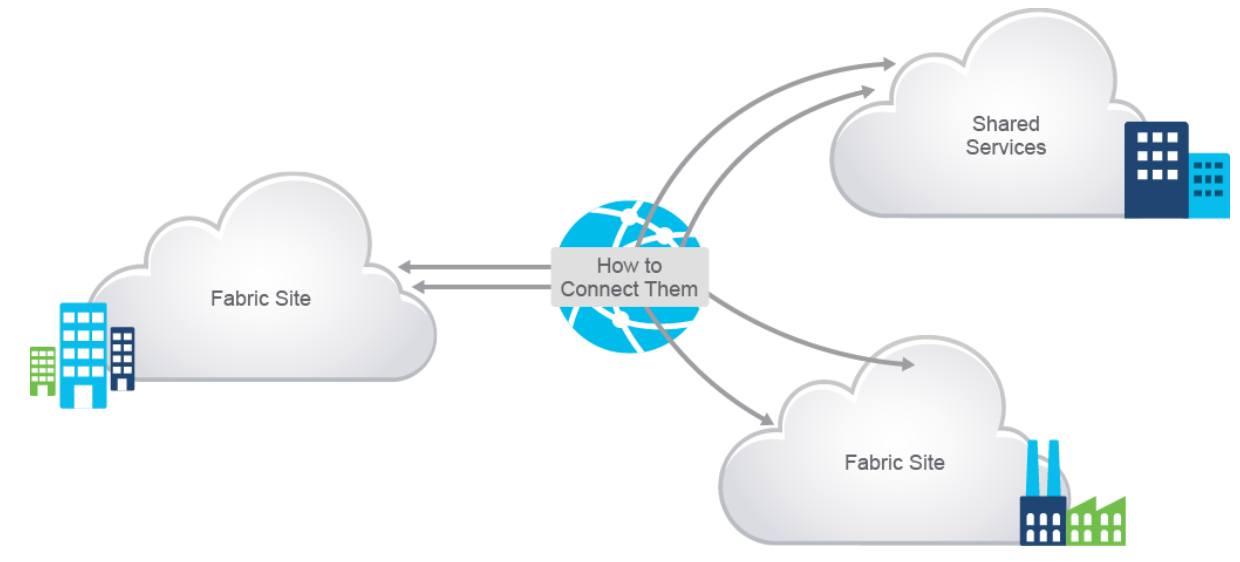
In your Cisco SD-Access Distributed Campus solution, you may interconnect several sites using the transit network.
To provide end-to-end network virtualization, you may need detailed planning to ensure the integrity of the VNs. Usually, there is a need to have some form of shared services that can be reused across multiple VNs. It is important that those shared services are deployed correctly to preserve the isolation between different VNs sharing those services. The use of a fusion router directly attached to the fabric border provides a mechanism for route leaking of shared services prefixes across multiple networks, and the use of firewalls provides an additional layer of security and monitoring of traffic between VNs.
Examples of shared services include:
- Wireless infrastructure: Radio frequency performance and cost efficiency is improved using common wireless LANs (single SSID) versus previous inefficient strategies of using multiple SSIDs to separate endpoint communication. Traffic isolation is achieved by assigning dedicated VLANs at the WLC and using dynamic VLAN assignment using 802.1X authentication to map wireless endpoints into their corresponding VNs.
- DHCP, DNS, and IP address management: The same set of infrastructure services can be reused if they have support for virtualized networks. This support includes special capabilities such as advanced DHCP scope selection criteria, full echoing of DCHP options, multiple domains, and support for overlapping addresses so that services are extended beyond a single network.
- Internet access: The same set of internet firewalls can be used for multiple VNs. If firewall policies must be unique for each VN, the use of a multi-context firewall is recommended.
- IP voice and video collaboration services: When IP phones and other unified communication devices are connected in multiple VNs, the call control signaling to the communications manager and the IP traffic between those devices must be able to traverse multiple VNs in the infrastructure.
Shared services are commonly deployed with the following solutions:
- In Cisco SD-Access for Distributed Campus and locations distributed across the WAN, services are often deployed at on-premise data centers. These data centers are commonly connected to the core or distribution layers of a centralized location such as headquarters. Traffic is sent from the remote and branch sites back to the headquarters, and then directed toward the necessary services.
- Services may be local to the location. For survivability purposes, a services block may be established at each fabric-site location. Local services ensure that these critical services are not sent across the WAN or MAN and ensure that the endpoints are able to access them, even in the event of congestion or downlinks in the WAN. However, this also requires a fusion router per location to provide access to the shared services.
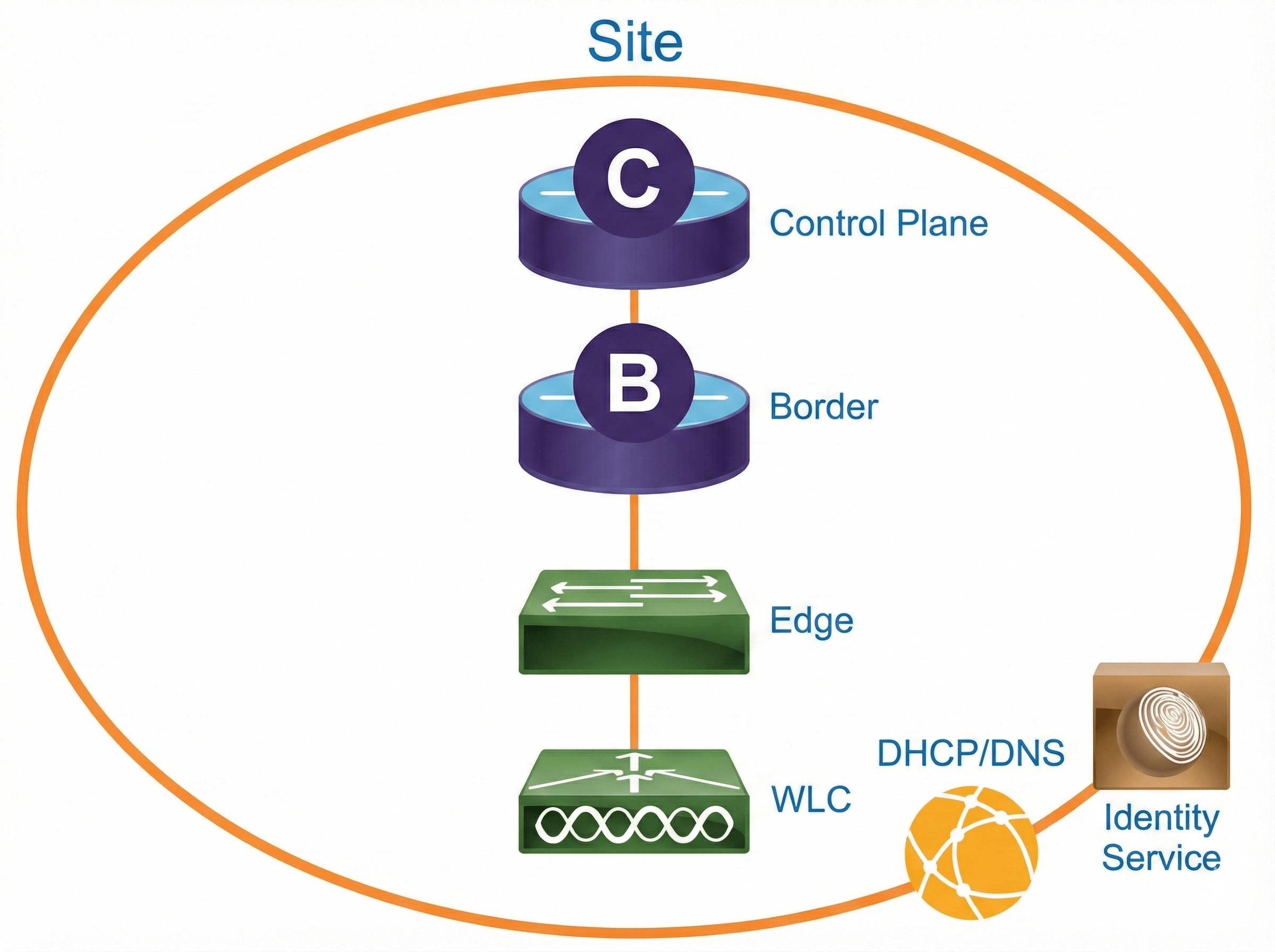
Cisco SD-Access Fabric Sites
A fabric site is an independent area with a unique set of fabric nodes: control plane, border, edge, WLC, and Cisco ISE Policy Service Node (PSN). Cisco ISE policy nodes are also distributed across the sites to meet survivability requirements.
The fabric site design can change based on the site size. To better understand common site designs, simple reference categories are used. It can be very useful to make the design easier and to understand how scalable your solution is. The numbers are used as guidelines only and do not necessarily match any specific limits for devices within a design.
Very small site uses Fabric in a Box to cover a single wiring closet, with resilience supported by switch stacking. It is designed for less than 2000 endpoints, less than 8 VNs, and less than 100 APs. The border, control plane, edge, and wireless functions are collocated on a single redundant platform.
Small site covers a single office or building. It is designed to support less than 10,000 endpoints, less than 32 VNs, and less than 200 APs. The border is collocated with the control plane function on one or two devices, and a separate wireless controller has an optional high-availability configuration.
Medium site covers a building with multiple wiring closets, or multiple buildings. It is designed to support less than 25,000 endpoints, less than 64 VNs, and less than 1000 APs. The border is distributed from the control plane function using redundant devices, and a separate wireless controller has a high-availability configuration.
Large site covers a large building with multiple wiring closets, or multiple buildings. It is designed to support less than 50,000 endpoints, less than 64 VNs, and less than 2000 APs. Multiple border exits are distributed from the control plane function on redundant devices, and a separate wireless controller has a high-availability configuration.
A fabric site may cover a single physical location, multiple locations, or just a subset of a location. These are examples of fabric site locations:
- Single location: branch or campus
- Multiple locations: metro campus and multiple branches
- Subset of a location: building or area within the campus
Cisco SD-Access Fabric Domains
A site is a fabric on its own control plane, edge, and border nodes. You may have several sites in your Cisco SD-Access network. A single fabric domain can consist of many individual sites within the fabric domain. These sites must be connected to allow inter-site communication within a particular fabric domain. The sites can be connected using a transit site.
In a fabric domain, you may have several fabric sites and a transit site to connect them. The transit site can be of different types, based on the technology used for the transit network. A key point about the transit site is that it has a fabric-wide control plane node that facilitates inter-site communication.
Transit Network
Transits are simply the physical connections between fabric sites. This connectivity may be a MAN, a WAN, or the internet. The WAN could be MPLS, Intelligent WAN (IWAN), or another WAN variation.
Within Cisco DNA Center, the transits are referred to as IP-based, Cisco SD-Access, or SD-WAN transits:
- IP-based transit: Leverages a traditional IP-based (VRF-Lite, DMVPN) network, which requires remapping of VRFs and SGTs between sites.
- Cisco SD-Access transit: Enables a native Cisco SD-Access (VXLAN, SGT) fabric, with a domain-wide control plane node for inter-site communication.
- Cisco SD-WAN transit: Leverages the Cisco SD-WAN as transit and carries the context in the Cisco SD-WAN encapsulation.
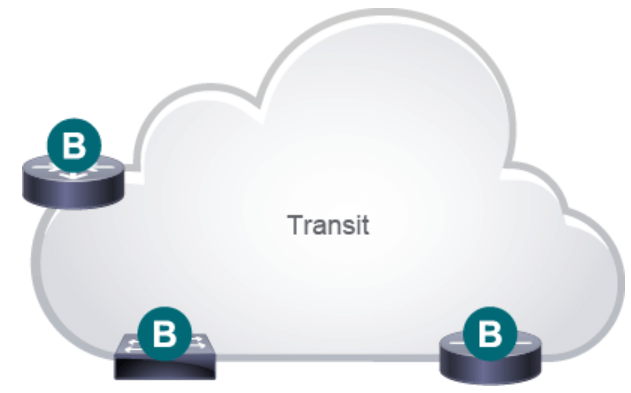
There must be IP reachability between fabric sites. Specifically, there must be a known underlay route between the loopback 0 interfaces on all fabric nodes. Existing BGP configurations and peering on the transit control plane nodes can have complex interactions with the configuration provisioned by Cisco DNA Center and should, therefore, be avoided. BGP private AS 65540 is reserved for use on the transit control plane nodes and is automatically provisioned by Cisco DNA Center. The transit control plane nodes should have IP reachability to the fabric sites through an IGP before being discovered or provisioned.
IP-Based Transit
In IP-based transits, packets are de-encapsulated from the fabric VXLAN into native IP. Once in native IP, they are forwarded using traditional routing and switching modalities. In Cisco DNA Center, IP-based transits are provisioned with VRF-Lite to connect to the upstream device. IP-based transits are used in two ways: connecting to shared services via fusion routers and connecting to upstream routing infrastructure for connectivity to WAN and the internet.





LEAVE A COMMENT
Please login here to comment.