EMAIL SUPPORT
dclessons@dclessons.comLOCATION
USEnterprise Network Access Control and Policy Enforcement using Cisco ISE
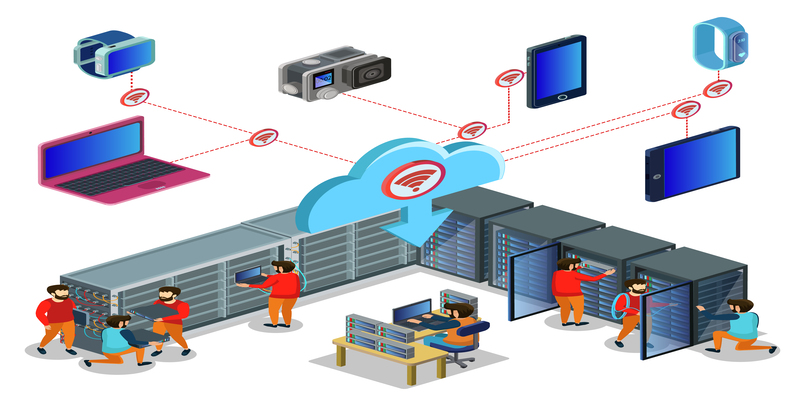
Modern enterprise networks aren't restricted to just a handful of employees and their devices. Companies today have a wide array of devices, including mobile devices, laptops, IoT equipment, and remote users who connect from multiple places. Making sure that secure access is available to all of these devices is a major issue for administrators of networks.
Traditional security models based on perimeters are no longer enough. Instead, companies require security models that are based on identity to examine devices, users, and policies prior to granting access to network resources. This method is often known as Network Access Control (NAC).
A single of the popular NAC platform can be found in the Cisco Identity Services Engine. It offers central authentication, authorization, and enforcement of policies across wireless, wired, and VPN networks. In this blog, we'll examine the concept of NAC and give an overview of ISE, explain how it works, and outline the key advantages and features of the platform that make Cisco ISE a critical component of security in the enterprise network.
Learning platforms like DClessons aid network engineers in understanding the technology in detail through structured learning and practical situations.
The Growing Need for Identity-Based Network Security
Enterprise networks are today able to accommodate thousands of users and devices that connect to multiple locations. They can be connected to branches, internal offices, and remote VPN sessions and wireless networks. Without a central system to manage access, businesses face serious security threats.
Identity-based access control can solve this issue by verifying the identity of both users and devices prior to granting access to network resources. Instead of allowing every connected device, network administrators could apply security policies based on the characteristics of identity, such as roles, posture of the device, as well as location and authentication methods.
This is the point where a contemporary NAC solution is essential. NAC platforms make sure that each device that connects with the network has been authenticated and authorized, and complies with security guidelines.
ISE Introduction: What Cisco Identity Services Engine Is
The first step in understanding modern security for networks is an extensive overview of ISE.
Cisco Identity Services Engine is a central network security policy platform that is designed to offer access control using identity. It allows organizations to create security policies that control who is able to access networks and what resources they are able to access, and under which circumstances access is allowed.
Cisco ISE collects contextual information about endpoints and users. This includes information about the identity of the user, the type of device, its position status, location, and the authentication method. Based on these parameters, the platform is able to apply dynamic policies to allow or block access to networks.
Since Cisco ISE integrates with multiple authentication and identity repositories. Organizations can manage access policies through one management console. This central architecture makes it much easier to manage the security of networks.
Many engineers learn about this technology by taking a Cisco ISE Introduction course, which describes the components, architecture, and actual use cases of access control for networks based on identity.
Evolution of Network Access Control: From Cisco NAC to Cisco ISE
Before the introduction of Cisco ISE, companies depended on older NAC technology to control network access.
One of the technologies used was one such technology was the Cisco Network Admission Control system. The system utilized an 802.1X authentication framework, and it was integrated with network services in order to verify endpoint security prior to granting access.
While the Cisco NAC product introduced significant ideas in security, the solution also had limitations when it came to adaptability, flexibility, and integration capabilities. A lot of organizations struggled to integrate NAC in large corporate environments.
In 2011, Cisco announced Cisco ISE as the next-generation NAC solution. The new platform dramatically improved security for identity-based users by offering:
* Centralized policy management
* More seamless connection to enterprise identification services.
* Improved profile of the device and visibility to the endpoint
Advanced authorization and authentication capabilities
Since its first release, Cisco ISE has evolved into a robust security system that is compatible with various access technologies and is integrated with a variety of security tools.
How ISE Works in a Nutshell
Understanding the way Cisco ISE works in concise terms can help clarify its role in protecting the enterprise network.
If a device or user wants to access the internet, a device like a wireless controller, switch, or VPN gateway serves as a point of enforcement for policies. The gadget communicates with Cisco ISE to verify the identity of the endpoint or user.
The procedure typically is a series of steps:
A device tries to join the internet.
The network access device transmits an authentication request through Cisco ISE.
Cisco ISE validates the credentials by using an identity repository like Active Directory or LDAP.
The platform reviews security policies based on attributes of identity.
Access to information is either allowed or not permitted as per the policy guidelines.
This workflow lets organizations apply security policies that are dynamic instead of static configurations for networks.
Cisco ISE as a Modern NAC Solution
In the modern workplace, Cisco ISE serves as a complete NAC solution, regulating access to all network components.
The platform can be accessed via multiple methods and methods of access, such as:
* wired network authentication
* Wireless network authentication
* VPN connections via remote
* Guest Access Management
By combining identity recognition with central security, Cisco ISE enables organizations to adopt a zero-trust networking access system. With these types of models, each user and device needs to be verified prior to receiving access rights to networks.
Cisco ISE also helps organizations keep in compliance with security policies and regulatory requirements through the provision of comprehensive logs and reports.
Core Features and Benefits of Cisco ISE
Another factor that has led to the fact that Cisco ISE becoming a well-known enterprise security solution is because of its wide range of options. Here are a few of the top advantages and features of Cisco ISE.
Centralized Policy Management
Cisco ISE offers a single web-based interface that enables administrators to manage their authentication policies devices profiling, authorization rules, guest access, and endpoint compliance. This central approach makes it easier to manage security processes for the network and guarantees that policies are enforced.
Dynamic Policy Enforcement
The platform is able to support rules-based access control policies that analyze multiple aspects, such as the identity of the user, the type of device, the authentication method, as well as security status. These attributes let administrators develop flexible access policies that can be adapted to various network scenarios.
Integration with External Identity Systems
Cisco ISE integrates with several external identity repositories like the LDAP system, Active Directory, RADIUS services, and a certificate authority. This integration lets organizations reuse their existing identity infrastructure while also implementing central NAC policies.
Guest Lifecycle Management
Guest users, such as visitors, contractors, partners, or guests, typically require access for a short period to access networks. Cisco ISE provides automated guest lifecycle management that includes the registration and authentication of guest accounts, expiration, and access policies enforcement.
Device Onboarding and Endpoint Compliance
The platform comes with self-service onboarding portals that allow users to sign up for using their devices. Cisco ISE can also integrate with mobile device management platforms in order to confirm that devices comply with security standards prior to giving access.
AAA Services and Authentication Protocols in Cisco ISE
Cisco ISE provides comprehensive Authentication, Accounting, and Authorization services that are the basis of the network access control.
The platform is primarily based on its RADIUS protocol, which authenticates and allows network access to users. RADIUS facilitates the connection between network access devices and the central authentication server.
Cisco ISE also supports several authentication protocols, such as:
* PAP
* CHAP
* EAP-MD5
* PEAP
* EAP-FAST
* EAP-TLS
* EAP-TTLS
These protocols allow organizations to establish robust authentication systems that are tailored to their security requirements.
Accounting functions within Cisco ISE monitor the authentication of users, their activities, as well as policy enforcement decision-making, giving administrators insight into the behavior of network access.
Apart from the role of TACACS+ Protocols in Device Administration from RADIUS-based access management, Cisco ISE also supports TACACS+ protocols for device management.
TACACS+ is used primarily to authenticate administrators whenever they connect to network devices like switches, routers, or firewalls. It separates authentication, as well as authorization and accounting procedures, which allows administrators to create specific security policies for access.
If an administrator attempts to connect to a network device, the device is regarded in the role of an AAA server and transmits authorization requests to Cisco ISE using TACACS+. The platform validates the credentials of the administrator and decides the commands and configuration actions that are authorized.
This level of supervision assures that only authorized staff can modify network configurations and keep detailed records of administrative actions.
Why Cisco ISE Is Critical for Enterprise Security
The modern enterprise network requires sophisticated security options that go beyond simple authentication. Cisco ISE offers several key features that make it an essential component in enterprise environments.
First, it allows centralized access control using identity across wireless, wired, or VPN. This approach is unified and simplifies the management of policies and provides the same security standards.
The second is that Cisco ISE provides detailed visibility into the network's activity. Administrators can monitor user behavior; spot unauthorized access attempts and react quickly to security threats that could be a threat.
Thirdly, the platform allows the integration of various security software, allowing companies to build a complete security ecosystem that is safe for the network infrastructure and users.
Learning Cisco ISE through Structured Training
Since Cisco ISE is a complex enterprise security platform, appropriate training is crucial for network professionals looking to effectively implement it.
The structured learning programs that are offered by DClessons aid engineers in developing an understanding of the fundamentals of network security based on identity. The programs provide an introduction to the architecture features and actual deployment scenarios of Cisco ISE.
With the help of guided explanations and hands-on demonstrations, engineers will learn the ways NAC platforms function in the modern enterprise network and how they are a part of the overall security strategy.
Final Thoughts
As networks for enterprise continue to grow and support an increasing number of devices and users, access control using identity is now a crucial requirement for the security of networks.
Cisco ISE plays a critical part in this security model through its central policy management and authentication services and flexible access control across multiple networks. Its capability to connect with identity repository systems, enforce security policies, and also support RADIUS and TACACS+ protocols makes it an effective NAC solution for today's organizations.
For professionals in security and networking, having a good knowledge of Cisco ISE architecture and capabilities is vital to design robust and secure enterprise networks. The process of learning these concepts via well-structured training materials like the ones provided by DClessons can assist engineers in developing the knowledge required to manage security-related identity efficiently.
Frequently Asked Questions (FAQs)
What exactly is Cisco ISE, and why is it essential to ensure the security of networks?
Cisco Identity Services Engine is a central platform that controls network access on the basis of user identification, device information, and security policies. It aids organizations in enforcing authentication as well as authorization and compliance for wireless, wired, and remote connections.
What's the process for making Cisco ISE work in an enterprise network?
Cisco ISE operates by communicating with devices that access the network, which includes wireless controllers, switches, and VPN gateways. If a device or user is trying to join, it transmits an authentication request to Cisco ISE, which validates credentials and applies security rules prior to giving access.
What is the main difference between Cisco NAC and Cisco ISE?
Cisco NAC was an earlier security solution for network access that was based on 802.1X authentication. Cisco ISE replaced NAC in 2011 with improved scalability as well as centralized management of policies and a deeper interaction with Identity Systems.
What authentication protocols does Cisco ISE support?
Cisco ISE supports several authentication protocols, including PAP, CHAP, EAP-MD5, PEAP, EAP-FAST, EAPTLS, and EAP TTLS. These protocols allow organizations to implement secure authentication systems that are suited to the specific security needs of their clients.
How are TACACS+ protocols used in conjunction with Cisco ISE?
TACACS+ protocol is utilized to manage devices. When administrators log into network devices, the device transmits authentication requests to Cisco ISE using TACACS+. The platform checks the credentials of users and enforces authorization policies for administrators.
You might also find these blog posts interesting:
Secure Device Administration and Network Access Using AAA Architecture
Designing Enterprise-Class Hybrid Cloud Connectivity Using AWS Networking Services
Exploring Core AWS Networking and Messaging Concepts for Modern Cloud Architectures




LEAVE A COMMENT
Please login here to comment.